237 KiB
Release Notes
A minor or major Forgejo release is published every three months, with more patch releases in between depending on the severity of the bug and security fixes it contains.
A patch or minor release (e.g. upgrading from v7.0.0 to v7.0.1 or v7.1.0) does not require manual intervention. But major releases where the first version number changes (e.g. upgrading from v1.21 to v7.0) contain breaking changes and the release notes explain how to deal with them.
Upcoming releases (not available yet)
8.0.0
TBD
7.0.4
This is a security release. See the documentation for more information on the upgrade procedure.
In addition to the following notable bug fixes, you can browse the full list of commits included in this release.
-
Security:
- PR. Fixed: CVE-2024-24789: the archive/zip package's handling of certain types of invalid zip files differs from the behavior of most zip implementations. This misalignment could be exploited to create an zip file with contents that vary depending on the implementation reading the file.
- PR - (fix & test). Fixed: the OAuth2 implementation does not always require authentication for public clients, a requirement of RFC 6749 Section 10.2. A malicious client can impersonate another client and obtain access to protected resources if the impersonated client fails to, or is unable to, keep its client credentials confidential.
-
Bug fixes:
- backport - PR. Fixed:
forgejo migrate-storage --type actions-artifactsalways fails because it picks the wrong path. - backport - PR. Fixed: avatar files can be found in storage while they do not exist in the database.
- backport - PR. Fixed: repository admins are always denied the right to force merge and instance admins are subject to restrictions to merge that must only apply to repository admins.
- backport - PR. Fixed: non conformance with the Nix tarball fetcher immutable link protocol.
- backport - PR. Fixed: migrated activities (such as reviews) are mapped to the user who initiated the migration rather than the Ghost user, if the external user cannot be mapped to a local one. This mapping mismatch leads to internal server errors in some cases.
- backport - PR. Fixed: a v7.0.0 regression causes
[admin].SEND_NOTIFICATION_EMAIL_ON_NEW_USER=trueto always be ignored. - backport - PR. Fixed: using a subquery for user deletion is a performance bottleneck when using mariadb 10 because only mariadb 11 takes advantage of the available index.
- backport - PR. Fixed: a v7.0.3 regression causes the expanding diffs in pull requests to fail with a 404 error.
- backport - PR. Fixed: SourceHut Builds webhook fail when the
triggersfield is used. - backport - PR. Fixed: the label list rendering in the issue and pull request timeline is displayed on multiple lines instead of a single one.
- backport - PR - commit. Fixed: NuGet Package fails
choco info pkgnamewhenpkgnameis also a substring of another package Id. - backport - PR - commit. Fixed: "Git hooks of this repository seem to be broken." warning when pushing more than one branch at a time.
- backport - PR - commit. Fixed: automerge does not happen when the approval count reaches the required threshold.
- backport - PR - commit. Fixed: the
FORCE_PRIVATE=truesetting is not consistently enforced. - backport - PR - commit. Fixed: CSRF validation errors when OAuth is not enabled.
- backport - PR. Fixed: headlines in rendered org-mode do not have a margin on the top
- backport - PR. Fixed:
-
Localization:
7.0.3
This is a security release. See the documentation for more information on the upgrade procedure.
In addition to the following notable bug fixes, you can browse the full list of commits included in this release.
-
Container image upgrades
In the Forgejo v7.0.3 container images, the Git version was upgraded to 2.43.4 which includes fixes for multiple vulnerabilities. However, the vulnerabilities with a high impact can be exploited when Git is used in an environment (or Operating Systems) which is different from the Forgejo OCI image.
-
Security:
- PR. Fixed: CVE-2024-24788: a malformed DNS message in response to a query can cause the lookup functions to get stuck in an infinite loop.
- PR. Fixed: backticks in mermaid block diagram labels are not sanitized properly.
-
Bug fixes:
- PR. Fixed: migration of a repository from gogs fails when it is hosted at a subpath.
- PR. Fixed: when creating an OAuth2 application the redirect URLs are not enforced to be mandatory.
- PR. Fixed: the API incorrectly excludes repositories where code is not enabled.
- PR. Fixed: "Allow edits from maintainers" cannot be modified via the pull request web UI.
- PR. Fixed: repository activity feeds (including RSS and Atom feeds) contain repeated activities.
- PR. Fixed: uploading maven packages with metadata being uploaded separately will fail.
- PR. Fixed: the mail notification sent about commits pushed to pull requests are empty.
- PR. Fixed: inline emails attachments are not properly handled when commenting on an issue via email.
- PR. Fixed: the links to .zip and tar.gz on the tag list web UI fail.
- PR. Fixed: expanding code diff while previewing a pull request before it is created fails.
- PR. Fixed: the CLI is not able to migrate Forgejo Actions artifacts.
- PR. Fixed: when adopting a repository, the default branch is not taken into account.
- PR. Fixed: when using reverse proxy authentication, logout will not be taken into account when immediately trying to login afterwards.
- PR. Fixed: pushing to the master branch of a sha256 repository fails.
- PR. Fixed: a very long project column name will make the action menu inaccessible.
- PR. Fixed: a useless error is displayed when the title of a merged pull request is modified.
- PR. Fixed: workflow badges are not working for workflows that are not running on push (such as scheduled workflows, and ones that run on tags and pull requests).
-
Localization:
-
Gitea v1.21 compatibility
This section is for information only and does not require any action.
The semantic version of the Forgejo 7.0 releases are:
v7.0.0+gitea-1.22.0v7.0.1+gitea-1.22.0v7.0.2+gitea-1.22.0v7.0.3+gitea-1.21.11
Gitea v1.22 is not published yet as of 21 May 2024 and in reality all Forgejo v7.0 releases are compatible with Gitea v1.21.11. Advertising they will be compatible with an unpublished Gitea version was incorrect. The Gitea v1.22 release was anticipated to happen shortly after Forgejo v7.0 was published on 23 April 2024 because it was already in the late stages of its release candidate lifecycle. However, around 27 April, the Gitea release candidates were dropped and the release candidates restarted from the Gitea development branch.
7.0.2
This is a bug fix release. See the documentation for more information on the upgrade procedure.
In addition to the following notable bug fixes, you can browse the full list of commits included in this release.
- Bug fixes:
- PR: a v7.0.0 regression where subscribing to or unsubscribing from an issue in a repository with no code produced an internal server error.
- PR: a v7.0.0 regression makes all the refs sent in Gitea webhooks to be full refs and might break Woodpecker CI pipelines triggered on tag (
CI_COMMIT_TAGcontained the full ref). This issue has been fixed in themainbranch of Woodpecker CI as well. - PR: the webhook branch filter wrongly applied the match on the full ref for branch creation and deletion (wrongly skipping events).
- PR: toggling the WIP state of a pull request is possible from the sidebar, but not from the footer.
- PR: when mentioning a user, the markup post-processor does not handle the case where the mentioned user does not exist: it tries to skip to the next node, which in turn, ended up skipping the rest of the line.
- PR: excessive and unnecessary database queries when a user with no repositories is viewing their dashboard.
- PR: duplicate status check contexts show in the branch protection settings.
- PR: profile info fails to render german singular translation.
- PR: inline attachments of incoming emails (as they occur for example with Apple Mail) are not attached to comments.
7.0.1
This is a bug fix release. See the documentation for more information on the upgrade procedure.
In addition to the following notable bug fixes, you can browse the full list of commits included in this release.
- Bug fixes:
- PR: LFS data corruption when running the
forgejo doctor check --fixCLI command or setting[cron.gc_lfs].ENABLED=true(the default isfalse). - PR: non backward compatible change in the
forgejo admin user createCLI command. - PR: error 500 because of an incorrect evaluation of the template when visiting the LFS settings of a repository.
- PR:
GET /repos/{owner}/{name}API endpoint always returns an empty string for theobject_format_namefield. - PR: fuzzy search may fail with bleve.
- PR: LFS data corruption when running the
7.0.0
The complete list of commits included in the Forgejo v7.0.0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges origin/v1.21/forgejo..origin/v7.0/forgejo
- Regressions and workarounds:
- Running the
forgejo doctor check --fixCLI command or setting[cron.gc_lfs].ENABLED=true(the default isfalse) will corrupt the LFS storage. The workaround is to not run the doctor CLI command and disable thecron.gc_lfs. This regression will be fixed in 7.0.1. - The
forgejo admin user createCLI command requires a password change by default when creating the first user and the--adminflag is not specified. The--must-change-password=falseargument must be given to not require a password change. This regression will be fixed in 7.0.1.
- Running the
- Breaking changes requiring manual intervention:
- Forgejo webhooks now always send full refs (starting with
refs/) instead of sending short refs in some cases. This new behavior may require changes when the receiving end assumes a short ref will be received (for instance some versions of Woodpecker CI when receiving webhook payloads when a tag is set). - MySQL 8.0 or PostgreSQL 12 are the minimum supported versions. The database must be migrated before upgrading. The requirements regarding SQLite did not change.
- The
per_pageparameter is no longer a synonym forlimitin the /repos/{owner}/{repo}/releases API endpoint. - The date format of the
createdandlast_updatefields of the/repos/{owner}/{repo}/push_mirrorsand /repos/{owner}/{repo}/push_mirrors API endpoint changed to be timestamps instead of numbers. - Labels used by pprof endpoint have been changed:
graceful-lifecycletogracefulLifecycleprocess-typetoprocessTypeprocess-descriptiontoprocessDescriptionThis allows for those endpoints to be scraped by services requiring prometheus style labels such as grafana-agent.
- The repository description imposes additional restrictions on what it contains to prevent abuse. You may use the v7.0 test instance to check how it will be modified.
- The Gitea themes were renamed and the
[ui].THEMESsetting must be changed as follows:giteais replaced bygitea-lightarc-greenis replaced bygitea-darkautois replaced bygitea-auto
- Forgejo webhooks now always send full refs (starting with
- Breaking changes in the user interface:
Note that the modifications related to CSS, templates or assets (images, fonts, etc.) are not documented here.
Although they can be extracted and modified, Forgejo does not provide any guarantee that such changes
will be portable from one version to another (even a patch version). See also
the developer documentation about interface customization.
- Update checker setting might change. The documentation was listing it as enabled by default, however, for a while it was disabled unless it was explicitly specified in the config or on the installation page. Instances migrated from Gitea also had it disabled due to different default value. Since then Forgejo got a privacy-friendly DNS-based update checking mechanism which is now being enabled by default unless explicitly specified in the config.
- Language statistics for repositories that use
linguistattributes in.gitattributesmay show different statistics than previously, because Forgejo recognizes more linguist attributes now. - It is no longer possible to replace the default web editor used to write comments or issues and pull requests with the EasyMDE editor. It is however still available as an alternative to edit releases and wiki pages.
- The list of all repositories and the
New Issuebutton are no longer available in the user dashboard for issues and pull requests.
- Migration warning
- If the logs show a line like the following, run doctor convert to fix it.
[W] Current database is using a case-insensitive collation "utf8mb4_general_ci" - Large instances may experience slow migrations when the database is upgraded to support SHA-256 git repositories. For instance, here are the logs from a test migration of the https://codeberg.org production database:
[I] Migration[286]: Add support for SHA256 git repositories [W] [Slow SQL Query] ALTER TABLE `commit_status` MODIFY COLUMN `context_hash` VARCHAR(64) [] - 3m41.647738396s [W] [Slow SQL Query] ALTER TABLE `comment` MODIFY COLUMN `commit_sha` VARCHAR(64) [] - 1m5.500234133s [W] [Slow SQL Query] ALTER TABLE `release` MODIFY COLUMN `sha1` VARCHAR(64) [] - 22.06241145s
- If the logs show a line like the following, run doctor convert to fix it.
- Features and enhancements
- Repository settings have been refactored, lifting out the repository unit-related settings to their own page. (#2221)
- When additional units can be enabled, an "Add more..." link will be displayed for repository admins. This can be turned off. (#2533)
- Repository administrators can allow anyone to edit the wiki in the repository Settings. (#2001)
- Instance administrators can enable repository badges in the configuration file. This feature depends on a shield generator service such as shields.io, and is disabled by default. (#2070)
- Instance administrators can configure the additional clone methods displayed on the repository home view. (gitea#29320)
- Instance administrators can assign custom flags to repositories. This is disabled by default, and currently requires custom templates to do anything useful with the flags. (#2079 & #2097)
- Fallback for basic repo search using git-grep when code indexer is disabled (gitea#29998)
- Repository administrators can disable forking instance-wide by setting the new
[repository].DISABLE_FORKSsetting. (#2445) - Render permalinks to files with a line range by an inline preview in all places where markup is allowed (#2669)
- A user can now optionally set their preferred pronouns (#1518).
- Always enable caches.
- Forgejo now recognizes more linguist attributes, making it possible to include documentation in the repository language statistics, for example. (#2088)
- When displaying the message to open a pull request from a recently pushed branch, the recently pushed branch now links to the appropriate branch. (#2141)
- Users who signed up, but have not activated their accounts yet, are now able to change their email before activation. (#1891)
- The "You pushed on branch ...." banner is now displayed for repositories you have a fork of with recently pushed branches too (#2195), and it will no longer consider branches that share no history with the default branch. (#2196)
- Forgejo will now highlight signed tags in a similar way it highlights signed commits. (#2534)
- Forgejo gained support for the more recent GitHub-style alert blocks. (#2348)
- The older style remains supported too.
- [ACTIONS] Add vars context to cron jobs
- [ACTIONS] Allow viewing the latest Action Run on the web
- [AGIT] Automatically fill in the description
- [API] Add API to get PR by base/head
- [API] commentAssignment() to verify the id belongs
- [API] DELETE /repos/{owner}/{repo}/pulls/{index}/reviews/{id}/comments/{comment}
- [API] endpoint for adding comments to reviews
- [API] GET /repos/{owner}/{repo}/pulls/{index}/reviews/{id}/comments/{comment}
- [API] support for repository flags
- [I18N] Clarify description in deletion modal
- [I18N] Clarify the description of SSH Keys
- [I18N] Data size unit localization
- [I18N] Improve branch select list ui in go templates (gitea#29729)
- [I18N] Improve localization of repo summary
- [I18N] Improve registration / password reset emails
- [I18N] Use correct translations for pull request
- [I18N] Improve translatability of activity heatmap
- [I18N] Improve English locale for admin settings
- [I18N] Add plural support: 1, 2, 3, 4
- [I18N] General improvements to English locale: 1, 2, 3, 4, 5, 6.
- [I18N] Allow custom repo size format
- [PACKAGES] nuget basic manifest download
- [UI] Add label filters in organization issues dashboard
- [UI] Allow users to hide all "Add more units..." hints
- [UI] Display tag name as title for a tag with no release [gitea]
- [UI] Enable ambiguous character detection in configured contexts
- [UI] Improve display of 404/500 error pages
- [UI] Improve look of user profiles
- [UI] Include a branch link in the recently pushed banner
- [UI] Offer to remove WIP: prefix in sidebar
- [UI] Port console colors
- [UI] pulls "Edit File" button in "Files Changed" tab
- [UI] Remove add organization on dashboard switcher
- [UI] Restrict file size of blame operation
- [UI] Show follow symlink button
- [UI] split code conversations in diff tab
- [UI] Update look of repo/org tabs on homepage
- [UI] Visual separation between types of attachments
- [UI] [AGIT] Add AGit label to AGit-created PRs
- [UI] [AGIT] Add link to docs and tooltip to label
- Implement commit mail selection for other Git operations
- Improved Linguist compatibility
- improve nuget nuspec api
- Log SQL queries when the database return error
- New doctor check: fix-push-mirrors-without-git-remote
- New route to view latest run of specific workflows
- Check for Commit in opengraph
- Check if commit is already present in target branch
- Configure if protected branch rule should apply to admins
- Count downloads for tag archives
- depguard sha256-simd
- Don't consider orphan branches as recently pushed
- extend webfinger to respond to profile page URIs
- Highlight signed tags like signed commits
- Allow changing the email address before activation
- Allow changing the repo Wiki branch to main
- Allow forking without a repo ID
- Allow instance-wide disabling of forking
- Allow non-explicit push options
- Allow to exclude files in dump
- add bucket lookup type
- Add download URL for executable files
- Add gitignore template for Janet projects
- add optional storage init to doctor commands
- Add rel="nofollow" to issue filter links
- Add support for shields.io-based badges
- Add Zig gitignore
- Recognize SSH signed tags too
- Repository flags
- support
.forgejodir for issue and PR templates - Support Include/Exclude Filters for Grep
- Use 'Text' instead of 'Plaintext'
- Render code tags in commit messages.
- Refactor markdown attention render.
- Add default board to new projects, remove uncategorized pseudo-board.
- Add more stats tables.
- Improve branch select list ui in go templates.
- Update allowed attachment types.
- Completely style the webkit autofill.
- Set user's 24h preference from their current OS locale.
- Make wiki default branch name changeable.
- Make admin pages wider because of left sidebar added and some tables become too narrow.
- Make PR form use toast to show error message.
- Rename Action.GetDisplayName to GetActDisplayName.
- Unify search boxes.
- Detect broken git hooks.
- Filter for default-branch selection.
- Include resource state events in Gitlab downloads.
- Properly migrate target branch change GitLab comment.
- Recolor dark theme to blue shade.
- Unify organizations header.
- Auto-update the system status in admin dashboard.
- Show more settings for empty repositories.
- Downscale pasted PNG images based on metadata.
- Show
View at this point in historyfor every commit. - Drop "@" from email sender to avoid spam filters.
- Allow non-admin users to delete review requests.
- Some performance optimization on dashboard and issues page.
- Improve user search display name.
- Fix UI Spacing Errors in mirror settings.
- Include username in email headers.
- Also match weakly validated ETags.
- Propagate install_if and provider_priority to APKINDEX.
- Fix display latest sync time for pull mirrors on the repo page.
- Remove trust model selection from repository creation on web page because it can be changed in settings later.
- Add ability to see open and closed issues at the same time.
- Move sign in labels to be above inputs.
- Move the captcha script loader to the template which really needs it.
- Display latest sync time for pull mirrors on the repo page.
- Show in Web UI if file is vendored and generated.
- Add orphaned topic consistency check.
- Convert to url auth to header auth in tests.
- Add option to set language in admin user view.
- Fix incorrect run order of action jobs.
- Add missing exclusive in advanced label options.
- Add combined index for issue_user.uid and issue_id.
- Add edit option for README.md.
- Fix link to
Codetab on wiki commits. - Remove autofocus in search box.
- Allow to set explore page default sort.
- Improve PR diff view on mobile.
- Properly migrate automatic merge GitLab comments.
- Display issue task list on project cards.
- Add Index to pull_auto_merge.doer_id.
- Fix display member unit in the menu bar if there are no hidden members in public org.
- List all Debian package versions in
Packages. - Allow pull requests Manually Merged option to be used by non-admins.
- Only show diff file tree when more than one file changed.
- Show placeholder email in privacy popup.
- Revamp repo header.
- Add link to members and repositories at teams page.
- Add link for repositories README file.
- Add
must-change-passwordcli parameter. - Unify password changing and invalidate auth tokens.
- Add slow SQL query warning.
- Pre-register OAuth application for tea.
- Differentiate between
pushandpullmirror sync in progress. - Cargo package - Fix missing domain in cargo sparse url.
- Link to file from its history.
- Add a shortcut to user's profile page to admin user details.
- Doctor: delete action entries without existing user.
- Add anchor to review types.
- Show total TrackedTime on issue/pull/milestone lists.
- Improve commit record's ui in comment list.
- Don't show new pr button when page is not compare pull.
- Add
Hide/Show all checksbutton to commit status check. - Improvements of releases list and tags list.
- Support pasting URLs over markdown text.
- Customizable "Open with" applications for repository clone.
- Allow options to disable user deletion from the interface on app.ini.
- Extend issue template yaml engine.
- Filter Repositories by type.
- Implement code frequency graph.
- Implement recent commits graph.
- Show commit status for releases.
- Actions Artifacts v4 backend.
- Add merge style
fast-forward-only. - Retarget depending pulls when the parent branch is deleted.
- Add global setting how timestamps should be rendered.
- Add skip ci functionality
- Show latest commit for file.
- Allow to sync tags from admin dashboard.
- Add Profile Readme for Organisations.
- Implement contributors graph.
- Artifact deletion in actions ui.
- Add API routes to get runner registration token.
- Add support for forking single branch.
- Add support for sha256 repositories.
- Add admin API route for managing user's badges.
- Repository settings have been refactored, lifting out the repository unit-related settings to their own page. (#2221)
- Bug fixes:
- The repository home view will no longer redirect to external units. (#2064)
- User and Organization
.profilerepositories now search for aREADME.mdfile case insensitively. (#2090) - When viewing a file, the RSS feed link is only displayed when there is an RSS feed provided for the context: when viewing a file on a branch. (#2103)
- Repository topic searches are now correctly paged, which should make topic management on larger instances orders of magnitudes faster. (#2060)
- Mentioning a user in a comment or similar place ignores apostrophes now. (#2485)
- Setting the
[repository].DISABLE_STARSsetting totruedisables the functionality completely, rather than just hiding it from the user interface. - Forking a repository is now available at a predictable URL, and does not require knowing the repository id. (#2310)
- Issue and pull request templates can now be placed in a
.forgejodirectory, like workflows. (#2290) - [A11Y] Fix accessibility and translatability of repo explore counters
- [A11Y] Focus styling and fix Watch/Unwatch buttons
- [A11Y] Label Stars/Forks links in repo explore
- [A11Y] Taborder in repo explore
- [ACTIONS] add proper payload to scheduled events
- [ACTIONS] Do not update PRs based on events that happened before they existed
- [ACTIONS] GetScheduledMergeByPullID may involve a system user
- [ACTIONS] Link to Workflow in View
- [ACTIONS] the ref of a scheduled action is always the default branch
- [API] Adjust name of operation
- [API]
/api/v1/{owner}/{repo}/issue_templates - [API] Document correct status code for creating a tag
- [API] /api/forgejo/v1/version auth check
- [API] inconsistencies
- [API] /issues/search endpoint
- [API] Make HTTPS schema default for Swagger
- [I18N] Add missing translation for more_items
- [I18N] Eliminate wrapping quotes in English locale
- [I18N] English fixes and improvements
- [I18N] Fix milestone sorting translation keys
- [I18N] Use correct translation on closed milestones
- [I18N] Use new translation key
- [PACKAGES] Delete redundant snap packaging recipe
- [PACKAGES] Fix Alpine Registry packages with noarch not being found
- [PACKAGES] Generate install if condition for Alpine
- [PACKAGES] Packagist webhook: support all events
- [PACKAGES] Fix for PyPi Registry PEP 503 Compliance
- [UI] Adjust the signed tag verification line
- [UI] Better color for labels/counters
- [UI] Better number for UserCards pagination
- [UI] Center icon and callout text
- [UI] Consistent styling for Sort filter
- [UI] Disable the RSS feed in file view for non-branches
- [UI] Disable 'View at this point in history' for wikis
- [UI] Display error message if doer is unable to fork
- [UI] Don't use
<br />in alert block - [UI] Fix admin layout
- [UI] Fix crash in issue forms
- [UI] Fix Ctrl+Enter on submitting review comment
- [UI] Fix diff patch operation in web UI
- [UI] Fixes for project selector in sidebar
- [UI] Fix must-change-password help dialog
- [UI] Fix relative links on orgmode
- [UI] Fix selector inner radius
- [UI] Fix tone of callout boxes for Forgejo dark
- [UI] Fix tooltip for 1000+ stars/forks
- [UI] include hostname in admin panel URL in new user emails
- [UI] Increase contrast of code block
- [UI] Limit amount of javascript errors being shown
- [UI] Make settings tab not active when on repository "Add units" tab
- [UI] Make write and preview tabs interactive
- [UI] New issue button position consistency
- [UI] Fix orgmode link resolver for text descriptions
- [UI] Preview: set font-size on preview content
- [UI] Fix primary button background inconsistency
- [UI] Fix regression of issue edit not working
- [UI] Fix relative links rendering
- [UI] Remember topic only in repo search
- [UI] Remove min-height from wiki elements
- [UI] Render emojis in labels in issue info popup
- [UI] Render correct label link
- [UI] Render inline file permalinks
- [UI] Fix repo badges when the label or text contains dashes
- [UI] Fix repo unarchivation button
- [UI] Restrict when to make link absolute in markdown
- [UI] Revert darker tone on labels
- [UI] Simplify converting struct to map in admin stats
- [UI] Fix the Fork button in repo headers
- [UI] Use correct logout URL
- [UI] Use separate keys for tabs on login screen
- [UI] "view file" button in diff compare view
- add Cache-Control header for health-check
- add max idle time setting for db connections
- Allow
'sin mentions - Avoid
WHERE INfor comment migration query - Cleanup characters forbidden on Windows from test fixture filenames
- Correct changed files for CODEOWNERS
- Correct default licenses to work as desired
- Detect protected branch on branch rename
- Disabling Stars should disable the routes too
- doctor: Don't say All done when no checks were run
- Do not allow deletion of internal references
- Don't color dot literal color names
- Don't delete inactive emails explicitly
- Don't overwrite protected branch accidentally
- Don't redirect the repo to external units
- Don't remove builtin OAuth2 applications
- Ensure
HasIssueContentHistorytakes into accountcomment_id - Find README.md for user profiles case insensitively
- Fix header name in swagger response
- Fix pull request reopen conditions
- Fix unblock action
- Fix VSCode settings
- Gracefully handle missing branches on a repos branches page
- Initialize Git for hook regeneration
- Internal Server Error when resolving comments
- Load
AllUnitsEnabledwhen necessary - Makefile: check git diff exitCode
- Make pprof labels conformant with prometheus spec
- Make reference URL absolute
- misleading comparisons when comparing branches
- Block issue creation when blocked by repo owner
- NPE in
ToPullReviewList - NPE in
UsernameSubRoute - Only pass selected repository IDs to pagination
- panic in
canSoftDeleteContentHistory - prevent removing session cookie when redirect_uri query contains ://
- pull_request_template branch link
- Rate limit pre-activation email change separately
- Refactor LFS GC functions
- Reflect Cargo index state in settings
- Remember topic only in repo search
- Require Latex code to have a end sequence
- Respond with JSON Resource Descriptor Content-Type per RFC7033
- Fix session generation for database
- Sort file list case insensitively
- Fix the topic search paging
- Typo fix & clarify RegistrationToken
- Update checker setting updates
- Use correct format for attr-check error log
- Use correct head commit for CODEOWNER
- Use correct template for commitmail error
- Workaround borked Git version
- Remove scheduled action tasks if the repo is archived.
- Relax generic package filename restrictions.
- Prevent re-review and dismiss review actions on closed and merged PRs.
- Add a warning for disallowed email domains.
- Skip email domain check when admins edit user emails.
- Skip email domain check when admin users adds user manually.
- Add support for API blob upload of release attachments.
- Allow options to disable user gpg keys configuration from the interface on app.ini.
- Allow options to disable user ssh keys configuration from the interface on app.ini.
- Fix content size does not match error when uploading lfs file.
- Add API to get merged PR of a commit.
- Add API to get PR by base/head.
- Add attachment support for code review comments.
- Add support for action artifact serve direct.
- Show whether a PR is WIP inside popups.
- Add artifacts v4 jwt to job message and accept it.
- Fix some RPM registry flaws.
- Add branch protection setting for ignoring stale approvals.
- Added instance-level variables.
- Fix the wrong HTTP response status code for duplicate packages.
- Don't run push mirrors for archived repos.
- Support for grouping RPMs using paths.
- Fixes #27605: inline math blocks can't be preceded/followed by alphanumerical characters.
- Fix GPG subkey verify.
- Include encoding in signature payload.
- Fix milestoneID filter bug in issue list.
- Fix Citation modal responsiveness and clipboard copy.
- Fix incorrect locale Tr for gpg command.
- Improve a11y document and dropdown item.
- Determine fuzziness of bleve indexer by keyword length.
- Fix ellipsis button not working if the last commit loading is deferred.
- Fix incorrect diff expander for deletion of last lines in a file.
- Do not exceed display for the PR page buttons on smaller screens.
- Move citation button to proper place.
- Expire artifacts before deleting them physically.
- Fix can not select team reviewers when reviewers is empty.
- Fix default avatar image size in PR diff page.
- Fix branch list bug which displayed default branch twice.
- Set the
isPermaLinkattribute tofalsein theguidsub-element. - Fix long package version names overflowing.
- Fix wrong link in user and organization profile when using relative url.
- Fix session key conflict with database keyword.
- Fix commit status in repo list.
- Fix incorrect action duration time when rerun the job before executed once.
- Fix missing mail reply address.
- Filter inactive auth sources.
- Refactor Find Sources and fix bug when view a user who belongs to an inactive auth source.
- Fix issue not showing on default board and add test.
- Improve file history UI and fix URL escaping bug.
- Fix ldap admin privileges update bug.
- other
- [PERFORMANCE] git check-attr on bare repo if supported
- [REFACTOR] [AGIT] Refactor the AGit code
- [REFACTOR] generation of JWT secret
- [REFACTOR] PKT protocol
- Remove .exe suffix when cross-compiling on Windows.
- Refactor repo header/list.
- Update register application URL for GitLab.
- Update golang links to use https.
- Teams: new View button.
- Commit-Dropdown: Show Author of commit if available.
- Refactor dropzone.
- When the title in the issue has a value, set the text cursor at the end of the text..
- Load citation JS only when needed.
- Refactor markdown attention render.
- Light theme color enhancements.
- Dark theme color enhancements.
- Refactor markup/csv: don't read all to memory.
- Move all login and account creation page labels to be above inputs.
- Fix Gitpod logic of setting ROOT_URL.
- Fix broken following organization.
- Don't do a full page load when clicking
WatchorStar. - Fix non-alphabetic sorting of repo topics.
- Make cross-reference issue links work in markdown documents again.
- Fix tooltip of variable edit button.
- Disable query token param in integration tests.
- Add merge arrow direction and update styling.
- Add links to owner home page in explore.
- Render PyPi long description as document.
- Ignore temporary files for directory size.
- Make pushUpdate error verbose.
- Add download URL for executable files.
- Improve profile for Organizations.
- Fix Show/hide filetree button on small displays.
- Fix merge base commit for fast-forwarded GitLab PRs.
- Align ISSUE_TEMPLATE with the new label system.
- Improve the list header in milestone page.
1.21.11-2
The complete list of new commits included in the Forgejo v1.21.11-2 release can be reviewed here, or from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo
$ git -C forgejo log --oneline --no-merges v1.21.11-1..v1.21.11-2
This stable release contains a security fix.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
6.0.13+0-gitea-1.21.10 -
Security fix
- PR. Fixed: the OAuth2 implementation does not always require authentication for public clients, a requirement of RFC 6749 Section 10.2. A malicious client can impersonate another client and obtain access to protected resources if the impersonated client fails to, or is unable to, keep its client credentials confidential.
1.21.11-1
This stable release contains a single bug fix for a regression introduced in v1.21.11-0 by which creating a tag via the API would fail with error 500 on a repository a where Forgejo Actions workflow triggered by tags exists.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
6.0.12+0-gitea-1.21.10 -
Bug fix
1.21.11-0
The complete list of new commits included in the Forgejo v1.21.11-0 release can be reviewed here, or from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo
$ git -C forgejo log --oneline --no-merges v1.21.10-0..v1.21.11-0
This stable release contains bug fixes and security fixes.
-
Recommended Action
We strongly recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
6.0.11+0-gitea-1.21.10 -
Security fix
- Fixed a privilege escalation through git push options that allows any user to change the visibility of any repository they can see, regardless of their level of access.
- Fixed a bug that allows user-supplied, non-sandboxed JavaScript to be run from the same domain as the forge, via
/{owner}/{repo}/render/branch/{branch}/{filename}URLs.
-
Bug fixes
- Use system action user to trigger scheduled action workflows
- Close file in upload function
- Prevent registering runners for deleted repositories. Prevents 500 Internal Server Error in admin interface.
- More reliable pagination support when migrating from gitbucket
- Fix automerge when used with actions
1.21.10-0
The complete list of commits included in the Forgejo v1.21.10-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.21.8-0..v1.21.10-0
This stable release contains bug fixes and a security fix.
Note that there is no Forgejo v1.21.9-0 release. The release numbering of the Forgejo v1.21 patch series follows the Gitea release numbering. However, the publication of Gitea v1.21.9 and Gitea v1.21.10 were a few days apart because of a regression that is not present on Forgejo and there was no need to publish Forgejo v1.21.9-0.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
6.0.10+0-gitea-1.21.10 -
Built with Go 1.21.9 and
golang.org/x/netv0.23.0It includes vulnerability fixes.
- CVE-2023-45288 which permits an attacker to cause an HTTP/2 endpoint to read arbitrary amounts of header data, all associated with a request which is going to be rejected. These headers can include Huffman-encoded data which is significantly more expensive for the receiver to decode than for an attacker to send. A Forgejo instance is affected if it is configured to listen to HTTPS instead of doing this via a reverse proxy.
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Fix to not remove repository avatars when the doctor runs with --fix on the repository archives.
- Detect protected branch on branch rename. If a branch cannot be renamed due to a protected branch rule, show this error in the UI instead of throwing an internal server error.
- Don't delete inactive emails explicitly. This can cause issues as the associated user might not have been deleted. It would lead to a database inconsistency and internal server errors if the user tries to activate their account.
- Fix user interface when a review is deleted without refreshing.
- Fix paths when finding files via the web interface that were not escaped.
- Respect
DEFAULT_ORG_MEMBER_VISIBLEsetting when adding creator to org. - Fix duplicate migrated milestones.
- Fix inline math blocks can't be preceded/followed by alphanumerical characters.
1.21.8-0
The complete list of commits included in the Forgejo v1.21.8-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.21.7-0..v1.21.8-0
This stable release contains bug fixes.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated to
6.0.8+0-gitea-1.21.8 -
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Fix
/api/v1/{owner}/{repo}/issue_templateswhich was always failing with a 500 error. - Prevent error 500 on /user/settings/security when SignedUser has a linked account from a deactivated authentication source.
- Fix error 500 when pushing release to an empty repo.
- Fix incorrect rendering csv file when file size is larger than UI.CSV.MaxFileSize.
- Fix error 500 when deleting account with incorrect password or unsupported login type.
- handle user-defined
nameanchors like[Link](#link)linking to<a name="link"></a>Link. - Use correct head commit for CODEOWNER.
- Fix manual merge button.
- Make meilisearch do exact search for issues.
- Fix PR creation via api between branches of same repo with head field namespaced.
- Fix
1.21.7-0
The complete list of commits included in the Forgejo v1.21.7-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.21.6-0..v1.21.7-0
This stable release contains bug fixes and a security fix.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
6.0.7+0-gitea-1.21.7 -
Built with Go 1.21.8
It includes vulnerability fixes.
- CVE-2023-45290 which could lead to memory exhaustion when parsing a multipart form.
- CVE-2023-45289 which could allow incorrect forwarding of sensitive headers and cookies on HTTP redirect.
-
Security fix
- The google.golang.org/protobuf module was bumped to version v1.33.0 to fix a bug in the google.golang.org/protobuf/encoding/protojson package which could cause the Unmarshal function to enter an infinite loop when handling some invalid inputs. Read more in the announcement.
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
1.21.6-0
The complete list of commits included in the Forgejo v1.21.6-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.21.5-0..v1.21.6-0
This stable release contains bug fixes and a security fix, as explained in the v1.21.6-0 companion blog post.
-
Recommended Action
We strongly recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
6.0.6+0-gitea-1.21.6 -
Security fix
- Fix XSS vulnerabilities. It enabled attackers to inject client-side scripts into web pages displayed to Forgejo visitors.
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Always write proc-receive hook for all git versions.
- Fix debian InRelease Acquire-By-Hash newline.
- Fix missing link on outgoing new release notifications.
- Workaround to clean up old reviews on creating a new one.
- Fix push to create with capitalize repo name.
- In Markdown don't try to make the link absolute if the link has a schema that's defined in
[markdown].CUSTOM_URL_SCHEMES, because they can't be made absolute. - Fix Ctrl+Enter on submitting review comment.
- In Git version v2.43.1, the behavior of
GIT_FLUSHwas accidentally flipped. This causes Forgejo to hang on thecheck-attrcommand, because no output was being flushed. Workaround this by detecting if Git v2.43.1 is used and setGIT_FLUSH=0thus getting the correct behavior. - When setting
url.hoston a URL object with no port specified (like is the case of default port), the resulting URL's port will not change. Workaround this quirk in the URL standard by explicitly setting port for the http and https protocols. - Fix elasticsearch Request Entity Too Large.
- Do not send update/delete release notifications when it is in a draft state.
- Do not run Forgejo Actions workflows synchronized events on the same commit as the one used to create a pull request.
- Fix a MySQL performance regression introduced in v1.21.4-0.
- Fix Internal Server Error when resolving comments.
- Packages
- org-mode files
1.21.5-0
The complete list of commits included in the Forgejo v1.21.5-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.21.4-0..v1.21.5-0
This stable release includes bug fixes as well as documentation improvements.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated to
6.0.5+0-gitea-1.21.5 -
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Upgrade go-git to v5.11.0. Although go-git is not used by Forgejo in a way that meets the requirements for the CVE-2023-49568 and DoS vulnerabilities to be possible, it is upgraded to v5.11.0 which mitigates the issue, as a precaution.
- Fix markdown relative links rendering
- Fix NPE in
UsernameSubRoute - Fix duplication when blocking multiple users
- Render code block in activity tab
- Fix reverting a merge commit failing
- Fix archive creating LFS hooks and breaking pull requests
- Avoid duplicate JS error messages on UI
- Fix incorrect PostgreSQL connection string for Unix sockets
- Fix avatar storage migration
- Prevent anonymous container access if
RequireSignInViewis enabled - Fix uploaded artifacts that were not overwritten
- Update enable_prune even if mirror_interval is not provided
- Strip
/from relative links
-
Improvements
1.21.4-0
The complete list of commits included in the Forgejo v1.21.4-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.21.3-0..v1.21.4-0
This stable release includes security and bug fixes as well as documentation improvements.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
Container image upgrades
In the Forgejo container images the ssh version was upgraded to 9.3_p2-r1 which includes a fix for CVE-2023-48795.
-
The semantic version was updated to
6.0.4+0-gitea-1.21.4 -
Security fixes
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Gracefully handle missing branches when a branch is missing from Git but still lingering in the database.
- Fix panic in
canSoftDeleteContentHistory - Check for Commit in opengraph
- Handle non-existent commit in Archive request
- Fix NPE in
ToPullReviewList - Fix URL in the mail to include the host
- Fix the event of a scheduled action to be "schedule" instead of a semi-random event from the default branch.
- Use refname:strip-2 instead of refname:short when syncing tags
- Fix button size in "attached header right"
- Fix
convert.ToTeamson empty input - Hide code related setting options in repository when code unit is disabled
- Fix incorrect URL for "Reference in New Issue"
- Fix panic when parsing empty pgsql host
- Fix alpine package files are not rebuilt
- Avoid cycle-redirecting user/login page
- Fix the scroll behavior for emoji/mention list
- Fix wrong due date rendering in issue list page
- Fix
status_check_contextsmatching bug - Fix 405 method not allowed CORS / OIDC
- Fix
GetCommitStatuses - Forbid removing the last admin user
- Fix issue dependencies
- Fix system webhooks API bug
-
Documentation
- The Forgejo Actions user reference guide includes event payload examples for pull requests and push events. It also covers most of the jobs syntax.
- The Forgejo command line page was entirely reworked and updates are now automated.
-
Improvements
1.21.3-0
The complete list of commits included in the Forgejo v1.21.3-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.21.2-1..v1.21.3-0
This stable release includes bug fixes. It was built with an updated version of the Go Cryptography package that fixes CVE-2023-48795. As explained in the corresponding Go issue: "The impact of this attack is relatively limited, as it does not compromise confidentiality of the channel."
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated to
6.0.3+0-gitea-1.21.3 -
Security fix
- The Go Cryptography package is upgraded to fix CVE-2023-48795.
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Fix a regression in how the markdown anchors are generated. For instance the anchor for
A.B.CisA-B-Cbut was incorrectly set toABC. - Fix the branch name of scheduled actions which was sometime incorrectly set.
- Fix a visual glitch when setting an emoji in the web UI.
- Recently Docker started to use the optional
POST /v2/tokenendpoint which should respond with a404 Not Foundstatus code instead of the current405 Method Not Allowed. - Fix a missing leading ssh:// when using a port other than 22 when Git URLs are displayed in the web UI.
- Allow disabling the detection of ambiguous unicode characters with the new setting
AMBIGUOUS_UNICODE_DETECTION=false. - Fix a regression with the issue references rendering in wiki pages.
- Fix merging artifact chunks error when minio storage basepath is set
- Fix missing information in the blame page web UI.
- Fix a regression in how the markdown anchors are generated. For instance the anchor for
1.21.2-1
The complete list of commits included in the Forgejo v1.21.2-1 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.21.2-0..v1.21.2-1
This stable release contains a security fix, as explained in the v1.21.2-1 companion blog post.
-
Recommended Action
We strongly recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
6.0.2+0-gitea-1.21.2 -
Security fix
The project page of private users is no longer publicly visible.
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- The default preferred licenses for the [repository].PREFERRED_LICENSES setting were incorrect and have been fixed to be
Apache-2.0andMIT. - A failed cron job can no longer cause the Forgejo instance to shutdown.
- A pull request merged by a workflow using the automatic token with the
auto mergeflag no longer cause an error 500 when displaying the pull request page. - Tentative fix for when the database branch cache is out of sync with the branches found in Git repositories. When in doubt it is recommended to click on
Sync missed branches from git data to databasesin the/admindashboard.
- The default preferred licenses for the [repository].PREFERRED_LICENSES setting were incorrect and have been fixed to be
1.21.2-0
The complete list of commits included in the Forgejo v1.21.2-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.21.1-0..v1.21.2-0
This stable release includes bug fixes. It was built with Go v1.21.5 that fixes CVE-2023-39326 which a malicious HTTP client can exploit to cause a server to automatically read a large amount of data. It allows for memory exhaustion in the situation that HTTP chunked encoding requests can reach Forgejo.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated to
6.0.1+0-gitea-1.21.2 -
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- OAuth2 uses the link_account page when the email or username is missing
- Avoid conflicts of issue and PR numbers in GitLab migration
- Only pass selected repository IDs to pagination
- Add download URL for executable files
- Fix Forgejo repositories migration to also include issues, prs etc.
- Fix template substitution bug preventing notifications to be sent on new user registration
- When searching for issues, require that all terms are matched instead of one of them
- Ignore temporary files when calculating the size of a repository
- Convert git commit summary to valid UTF8
- Fix incorrect default value of
[attachment].MAX_SIZE - Fix object does not exist error when checking citation file
-
Improvements
1.21.1-0
The complete list of commits included in the Forgejo v1.21.1-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges origin/v1.20/forgejo..origin/v1.21/forgejo
-
Forgejo Semantic Version: The semantic version was updated to
6.0.0+0-gitea-1.21.0because it contains breaking changes. -
Breaking: Note that the modifications related to CSS, templates or assets (images, fonts, etc.) are not documented here. Although they can be extracted and modified, Forgejo does not provide any guarantee that such changes will be portable from one version to another (even a patch version). A Q&A discussion is available to share tips and tricks. A new section was also added to the developer documentation about interface customization.
- If you have custom asset files, e.g. custom themes, inside
custom/public/*(css included), you need to transfer these files tocustom/public/assets/*for them to be detected. Read more in the documentation and the Q&A discussion dedicated to interface customization. - Git branches are stored in the databases to reduce the calls to a git process and improve performances. After upgrading, login as an admin, go to the
/adminpage and click run Sync missed branches from git data to databases. If this is not done there will be messages such asLoadBranches: branch does not existin the logs. - Some Forgejo CLI options have changed and scripts may need to be updated. For instance
--verboseis no longer a global option and is implemented on a per sub-command basis. Checkforgejo --helporforgejo docsfor more information. - Remove "CHARSET" config option for MySQL and always use "utf8mb4". It has been a requirement for years and specifying anything else is likely to cause issues. Existing MySQL databases still using
utf8can be converted using the CLI:forgejo doctor convert. - Restrict certificate type for builtin SSH server. This is a breaking change for setups where the builtin SSH server is being used and for some reason host certificates were being used for authentication.
- Set SSH_AUTHORIZED_KEYS_BACKUP to false by default. There is no automatic cleanup of these backups and can end up using a significant amount of disk space over time.
- The minimum RSA keylength is now 3072 instead of 2048.
- Prior to this release, a token scoped to read or write permissions on issues was allowed to access both issues and pull requests, regardless of the restrictions imposed to the team in which they belong. In a team it is possible to grant finer grained permissions, for instance to allow a user to access issues but not pull requests. These restrictions are now enforced and API calls that previously succeeded on
/api/v1/repos/{org}/{repo}/issuesor other endpoints common to both issues and pull requests could return 404. Granting the user the necessary permissions in the team in which they belong will allow them to use that endpoint again.
- If you have custom asset files, e.g. custom themes, inside
-
Forgejo Actions: It is now enabled by default but should still be considered alpha stage and subject to unannounced breaking changes.
- The API can now be used to manage secrets for users, organizations and repositories.
- Registration tokens can register multiple runners instead of a single one. Read more about runner registration.
- Add support for variables in addition to secrets.
- Add support for recurring actions similar to cron jobs.
- Add the possibility to disable workflows from the user interface.
- Add automatic cleanup of artificats.
- Add automatic cancellation of jobs when pushing new commits to a PR.
- Add support for uploading multiple artificats.
- Add support for the
pull_request_targetevent which has access to secrets because it runs using the workflows from the base branch instead of the pull request. - Add support for reading labels from the runner instead of specifying them during registration.
-
Features:
- With the Chroma upgrade from 2.7.0 to 2.10.0 syntax highlighting is now available for Smali, DHCP, WebGPU Shading Language, AutoHotkey, AutoIt, tal (uxntal), ArangoDB Query Language (AQL), BIND DNS Zone, Odin, Sourcepawn, CPP, C. New files and extensions are associated as follows: .tpp as a c++, .eex as a Elixir, Pipfile and poetry.lock as a TOML, ISCdhcpd filename, .twig, Mathematica.
- With the go-enry upgrade from v2.8.4 to v2.8.6, language detection in the repository now includes:
- Bluespec BH: atom-haskell/language-haskell
- D2: terrastruct/d2-vscode
- Go Workspace: golang/vscode-go
- Gradle Kotlin DSL: nishtahir/language-kotlin
- Hosts File: Alhadis/language-etc
- LOLCODE: KrazIvan/LOLCODE-grammar-vscode
- MDX: wooorm/markdown-tm-language
- Nasal: BobDotCom/Nasal.tmbundle
- Nushell: hustcer/nu-grammar
- Pact: kadena-io/pact-atom
- RBS: soutaro/vscode-rbs-syntax
- Rez: textmate/rez.tmbundle
- Sweave: textmate/sweave.tmbundle
- TL-Verilog: adamint/tlv-vscode
- Typst: michidk/typst-grammar
- WDL: broadinstitute/wdl-sublime-syntax-highlighter
- WGSL: wgsl-analyzer/wgsl-analyzer
- WebAssembly Interface Type: bytecodealliance/vscode-wit
- Newly pushed branches show in the web UI with a link to create a PR. Read more about the
New Pull Requestbutton. - Labels that are no longer useful can be archived. They can no longer be selected but they remain on existing issues. Read more about archiving labels.
- The blame view now takes into account the
.git-blame-ignore-revsfile. - Pre-register OAuth2 applications for git credential helpers. Read more in the git authentication section of the user guide and the administrator guide.
- Admins can be notified via email when a new user registers to help fight spam bots by setting
[admin].SEND_NOTIFICATION_EMAIL_ON_NEW_USER = true. - When a page display the history of changes for a file, file rename are detected and displayed.
- Packages can be configured to redirect requests to the S3 server for clients that support this feature.
- When a PR contains multiple commits, it is now possible review to each commit independently. Read more about selecting commits for review.
- Issues can be deleted in batch.
- An email can be associated with an Organisations.
- The CODEOWNERS file is interpreted to automatically set reviewers on PRs. The CODEOWNERS file is loaded from these paths in this order:
./CODEOWNERS,./docs/CODEOWNERS. - Issue search were reworked entirely to fix the shortcomings of the previous implementation.
- Allow "latest" to be used as a release tag when downloading a file.
- Authentication via reverse proxy is available and disabled by default.
- Add API for changing avatars.
-
User Interface:
- Show OpenID Connect and OAuth on the signup page.
- Show branches and tags that contain the commit being displayed
- Add 'Show on a map' button to the location in the usr profile.
- Render plaintext task list items for markdown files.
- The administrators user details page was modified.
- When mirroring a repository fails, a
Retrybutton allows to re-create it. - Package cleanup can be triggered from from administration web interface.
- In the page displaying the list of branches, it is now possible to search them by name.
- Display all user types (including bots) org types on the administration web interface.
- Improve opengraph previews.
- Render code blocks in the repository description.
- Add
member,collaborator,contributor, andfirst-time contributorroles and tooltips next to the author. - It is no longer possible to change the run user in the installation page.
- Update emoji set to Unicode 15.
- Improve the image diff user interface.
- Allow rebuilding the issue index from the cron task list in the admin panel.
-
Enhancements:
- Improve the privacy of the user profile settings.
- Add the upload URL to the release API.
- Allow editing existing push mirrors from the settings page of a repository.
- Add a link to the OpenID issuer URL in the WebFinger response.
- Support copy protected branches with template repositories.
- In the administration web interface, split the lfs size from repository size.
-
Bug fixes:
-
Security:
1.20.6-1
The complete list of commits included in the Forgejo v1.20.6-1 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.20.6-0..v1.20.6-1
This stable release contains a security fix.
-
Recommended Action
We strongly recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
5.0.8+0-gitea-1.20.6 -
Security fix
The project page of private users is no longer publicly visible.
-
Bug fix
- Consider executable files as a valid case when returning a downloadURL for them. They are just regular files with the difference being the executable permission bit being set.
-
New doctor check and fix
- Adds a new doctor check: fix-push-mirrors-without-git-remote. The new check looks for push mirrors that do not have their remotes configured in git. If automatic fixing is enabled, it will remove these push mirrors from the database.
1.20.6-0
The complete list of commits included in the Forgejo v1.20.6-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.20.5-1..v1.20.6-0
This stable release contains a security fix, as explained in the v1.20.6-0 companion blog post.
-
Recommended Action
We strongly recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
5.0.7+0-gitea-1.20.6 -
Breaking change
Prior to this release, a token scoped to read or write permissions on issues was allowed to access both issues and pull requests, regardless of the restrictions imposed to the team in which they belong. In a team it is possible to grant finer grained permissions, for instance to allow a user to access issues but not pull requests. These restrictions are now enforced and API calls that previously succeeded on
/api/v1/repos/{org}/{repo}/issuesor other endpoints common to both issues and pull requests could return 404. Granting the user the necessary permissions in the team in which they belong will allow them to use that endpoint again. -
Security fix
Additional API and web endpoints now fail when given manually crafted identifiers.
1.20.5-1
The complete list of commits included in the Forgejo v1.20.5-1 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.20.5-0..v1.20.5-1
This stable release contains critical security fixes, as explained in the v1.20.5-1 companion blog post.
-
Recommended Action
We strongly recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
5.0.6+0-gitea-1.20.5 -
Security fixes
- API and web endpoints now fail when given manually crafted identifiers.
- When an extension is added to the URL of a user profile (e.g.
/myuser.rss) it is now verified to be visible. docker loginnow fails with basic auth when 2FA is enabled.
-
Bug fixes
The most prominent bug fixes are described below. Others can be found in the list of commits included in the release as described above.
- Create the ActionTaskOutput table for new Forgejo instances.
- Restricted users only see repos in orgs which their team was assigned to.
- Release assets are now taken into account during a migration from GitLab, Forgejo or Gitea.
- When
webhook.PROXY_URLis set, theALLOWED_HOST_LISTsetting is now properly enforced. - It is now possible to access
/<username>/<reponame>/attachments/<uuid>with an application token and the attachments API download URL is usable.
1.20.5-0
The complete list of commits included in the Forgejo v1.20.5-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.20.4-1..v1.20.5-0
This stable release contains an important security fix, as explained in the v1.20.5-0 companion blog post.
-
Recommended Action
We strongly recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated to
5.0.5+0-gitea-1.20.5 -
Security fix
- When a user logs into Forgejo, they can click the Remember This Device checkbox and their browser will store a Long-term authentication token provided by the server, in a cookie that will allow them to stay logged in for an extended period of time. The implementation was inherently insecure and was reworked. Read more about this issue in the v1.20.5-0 blog post.
-
Bug fixes
The most prominent bug fixes are described below. Others can be found in the list of commits included in the release as described above.
- Fix the display of pull requests waiting for review on the
/pullspage. It incorrectly included all reviews. - Fix a v1.20 regression preventing access to files with OAuth2 tokens in private repositories.
- Fix a bug by which the
doctorcommand complains thedeleted_branchtable is missing although it should not. - Fix the release URL in webhooks so that
URLpoints to the API URL andHTMLURLpoints to the web page. - Fix organization field being null in POST /orgs/{orgid}/teams.
- Fix the display of pull requests waiting for review on the
1.20.4-1
The complete list of commits included in the Forgejo v1.20.4-1 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.20.4-0..v1.20.4-1
This stable release includes bug fixes.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated to
5.0.4+0-gitea-1.20.4 -
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
1.20.4-0
The complete list of commits included in the Forgejo v1.20.4-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.20.3-0..v1.20.4-0
This stable release includes bug fixes and two features.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated to
5.0.3+0-gitea-1.20.4 -
Features
- Log slow SQL queries to help identify bottlenecks on large Forgejo instances
- Add
branch_filterto hooks API endpoints
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Ignore the trailing slashes when comparing oauth2 redirect_uri
- Fix the reopen logic for agit flow pull request
- Fix the missing display of user projects
- Fix issue templates that failed to save checkboxes
- Fix accessibility issues preventing focus and selection
- Fix being unable to use a repo that prohibits accepting PRs as a PR source
- Forgejo doctor database fix to repair a condition preventing the owner of an organization from creating a repository
- Fix dashboard filters having no effect
- Also check the email blocklists when adding new emails to existing accounts
- Sync tags when adopting repos
- Fix an error when pushing a new branch and there is a requirement that all commits are signed
1.20.3-0
The complete list of commits included in the Forgejo v1.20.3-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.20.2-0..v1.20.3-0
This stable release includes bug fixes and a safeguard against a
regression that may lead to data loss. The [storage*] sections in the
app.ini file may cause the files for some subsystems - Attachments,
LFS, Avatars, Repository avatars, Repository archives, Packages - to
be merged together or misplaced. The safeguard detects this situation
and Forgejo will not start to prevent data loss. If your instance is in
this situation, follow the instructions in the companion blog post.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated to
5.0.2+0-gitea-1.20.3 -
Breaking changes
- Fix some bugs in how the storage sections are interpreted in the
app.inifile. Read more about this issue in the v1.20.3-0 blog post - Add sanity checks to detect an
app.iniconfiguration that needs manual fixing to preserve storage
- Fix some bugs in how the storage sections are interpreted in the
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Fix links to pull request reviews sent via mail. The pull request link was correct but it did not go the the review and stayed at the beginning of the page
- Recognize OGG as an audio format
- Consistently show the last time a cron job was run in the admin panel
- Fix NuGet registry v2 & v3 API search endpoints
- Allow html code to be parsed in markdown files
- Fix incorrect color of the selected assignees when creating an issue
- Add missing MinIO region on client initialization
- Add pull request review request webhook event
- Fix bad url in the wiki due to incorrect unescaping
- Fix the sort menu that was broken when displaying a custom profile from the
.profilerepository - Workaround MariaDB performance issue on large Forgejo instances
- Display human-readable text instead of numerical file modes
- The CLI exit code now is different from zero when an error occurs
- Fix error when a Debian package has a double newline character at the end of the control block
- Fix a condition that would cause git related tasks to hang for longer than necessary in the queues and use too many resources as a result
- Fix the topic validation rule and support dots
- Fix pull request check list when there are more than 30
- Fix attachment clipboard copy on insecure origin
- Fix the profile README rendering that was inconsistent with other markdown files renderings
- Fix API leaking the user email when the caller is not authentified
1.20.2-0
The complete list of commits included in the Forgejo v1.20.2-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.20.1-0..v1.20.2-0
This stable release includes bug fixes and displays warnings in the administration panel when deprecated entries are found in app.ini.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated to
5.0.1+0-gitea-1.20.2 -
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Add missing assets to the Forgejo sources tarball
- Fix user type selection error when creating a user and selecting
publicorprivate. - Fix access check for org-level project
- Warn instead of reporting an error when a webhook cannot be found
- Set MAX_WORKERS to a value lower than 10 if the number of available CPUs is low to avoid overloading the host.
- Fix bug when pushing to a pull request which enabled dismiss approval automatically
- Fix handling of plenty Nuget package versions
- Update email-setup.en-us.md
- Fix bugs in LFS meta garbage collection
- Fix UI regression of asciinema player
- Fix LFS object list style
- Fix CLI allowing creation of multiple user access tokens with the same name
- Fix router logger preventing separating the logs in different files.
- added ssh mirror workaround description
- Fix wrong workflow status when rerun a job in an already finished workflow
- Fix escape problems in the branch selector
- Fix handling of Debian files with trailing slash
- fix Missing 404 swagger response docs for /admin/users/{username}
- Use stderr as fallback if the log file can't be opened
1.20.1-0
The complete list of commits included in the Forgejo v1.20.1-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges origin/v1.19/forgejo..origin/v1.20/forgejo
- Forgejo Semantic Version:
The semantic version was updated to
5.0.0+0-gitea-1.20.1because it contains breaking changes. - Breaking:
- Scoped access tokens or (Personal Access Tokens), were refactored and although existing tokens are still valid, they may have a different scope than before. To ensure that no tokens have a larger scope than expected they must be removed and recreated.
- If your
app.inihas one of the the following[indexer].ISSUE_INDEXER_QUEUE_TYPE,[indexer].ISSUE_INDEXER_QUEUE_BATCH_NUMBER,[indexer].,[indexer].ISSUE_INDEXER_QUEUE_DIR,[indexer].ISSUE_INDEXER_QUEUE_CONN_STR,[indexer].UPDATE_BUFFER_LEN,[mailer].SEND_BUFFER_LEN,[repository].PULL_REQUEST_QUEUE_LENGTHor[repository].MIRROR_QUEUE_LENGTH, Forgejo will abort immediately. Unless you know exactly what you're doing, you must comment them out so the default values are used. - The
-poption ofenvironment-to-iniis no longer supported - The ".png" suffix for user and organizations is now reserved
- The section
[git.reflog]is now obsolete and its keys have been moved to the following replacements:[git.reflog].ENABLED→[git.config].core.logAllRefUpdates[git.reflog].EXPIRATION→[git.config].gc.reflogExpire
- The logger used to display Forgejo's was refactored and has new settings, different from the previous one found at
log.<mode>.<logger>inapp.ini. Check the documentation andapp.example.inifor more information. The SMTP logger was removed. - Forgejo will refuse to start if the refactored path & config system does not pass sanity checks (e.g. WORK_PATH must be absolute).
- Manually set WORK_PATH in
app.ini. If theapp.inifile is writable by the user under which the Forgejo server runs andWORK_PATHis not set, the server will add it. Otherwise it will log an error starting withUnable to update WORK_PATH. One of the consequences of not settingWORK_PATHinapp.iniis that pushing to a repository via ssh is likely to fail as explained in the corresponding bug report. Read the technical details in the commit that implements the WORK_PATH change. - The user profile can be customized with a Markdown file.
The profile page of a user is rendered using the
README.mdfile of the.profilerepository, if it exists. It is a breaking change because it will display the .profile/README.md of a pre-existing repository, private or not. - The API endpoint pagination for team members was fixed: it now starts at 1 instead of 0, just like all other paginated API endpoints.
- The
SSH_KEYGEN_PATHvariable inapp.ininow defaults to using the Go SSH key parsing instead of thessh-keygenbinary. WhenSTART_SSH_SERVERis true, the decision to use the Go SSH key parsing or an external binary will now depend on the value ofSSH_KEYGEN_PATHinstead of always using the Go SSH key parsing. - The storage settings were refactored. Read more about storage settings.
- The [repository.editor] PREVIEWABLE_FILE_MODES setting was removed. This setting served no practical purpose and was not working correctly. Instead a preview tab is always shown in the file editor when supported.
- In addition to the already deprecated options inside [queue], many options have been dropped as well. Those are WRAP_IF_NECESSARY, MAX_ATTEMPTS, TIMEOUT, WORKERS, BLOCK_TIMEOUT, BOOST_TIMEOUT, BOOST_WORKERS. You can remove them from your app.ini now. Additionally, some default values have changed in this section.
- The default CSS and templates included in Forgejo were heavily refactored and a large number of variables renamed. These changes are not documented and there is a very high chance that a template extracted and modified for a particular Forgejo instance will no longer work as it did. Browsing through the git history of the template in the sources is the best way to figure out how and why it was modified.
- Moderation: Blocking another user is desirable if they are acting maliciously or are spamming your repository. When you block a user, Forgejo does not explicitly notify them, but they may learn through an interaction with you that is blocked. Read more about blocking users.
- Package: New registries are available for SWIFT, debian, RPM, alpine, Go and CRAN.
- Accessibility: numerous improvements for issue comments, the menu on the navbar, scoped labels, checkboxes and dropdowns, RTL rendering support to Markdown, file (re-)views, interactive tooltips, using a button element, repository list and more.
- Time: The display and localization of time was improved for tooltips, milestones, due date and translations that contain dates, commit graphs, runners, webhooks, tests and more. Previously each rendered timestamp would be static, now the real time since an event happened is show. If a comment was added 2 minutes before the page rendered it would show as "2 minutes ago" on the initial render and if another 8 minutes have passed, without a page refresh you'd see "10 minutes ago".
- Wiki
- Improve the display of the table of content
- Fixed a bug preventing team users who have wiki write permission from deleting a page
- Shows the External Link icon and URL in the header to indicate that the user will be sent to an external side to help prevent fishing
- Allow dash in titles
- Actions
- The internal CI graduated from experimental to alpha. It now has with a user documentation that includes examples and an extensive administrator guide to set it up.
- Forgejo Actions workflows are now available to run tests and publish releases for
Forgejoitself. - The Woodpecker CI configuration for PR verification and building releases for Forgejo v1.18 and v1.19 is no longer maintained as part of Forgejo itself and was moved to its own repository.
- Templates
- User Interface and User eXperience
- The web editor used when creating issues, adding comments, etc. changed from EasyMDE which was no longer actively maintained to GitHub markdown. To help with the transition it is still possible to switch back to using EasyMDE using the double arrow button in the menubar.
- Improve wiki sidebar and TOC
- Show outdated comments in the files changed tab of a pull request review
- Redirect to package after version deletion
- Use a separate admin page to show stats
- Improve avatar compression and resizing
- Add button to compare force pushed commits in pull requests
- When creating a new file in a repository via the web user interface allow for a path to be pasted
- Allows "video" HTML tag to be used in MarkDown, with the src, autoplay, and controls attributes
- Add "Reviewed by you" filter for pull requests
- Make Ctrl+Enter submit a pending comment (starting review) instead of submitting a single comment
- If an instance chooses to disable new pull or push mirrors or mirrors entirely, an appropriate message will now be shown to the user in the Repository Settings
- Change
Closeto eitherClose issueorClose pull request - Make Issue/PR/projects more compact
- Improve RSS user interface
- Add details summary for vertical menus in settings to allow toggling
- Show visibility status of email in own profile
- Improve the protected branch setting page
- Improve the display of the pull request branch delete button
- Fix the color for repository transfer related buttons when having no permission to act
- Add a progressbar to Milestone Page
- Nicer display when the list of notifications is empty
- Rename board to column in projects
- Improve header bar on issue, pull requests and milestone
- Add organization visibility label when displayed on the dashboard
- Unification of registration fields order
- Append
(comment)when a link points at a comment rather than the whole issue - Add visibility (private, limited) in the dashboard navbar
- Show all activities in the dashboard, not just the most recent ones
- Do not display the stars in the repository list of the dashboard
- Improve the display of tags to include the tag message
- Hide the target selector if a tag exists when creating a new release
- Show the calculated commit status state of the latest commit on the default branch for each repository in the dashboard repository list
- Sort users and orgs on the explore page by recency
- Show the number of repositories in the user or organization profile
- Review management (requesting again and discard) now happens at the top of the pull request
- Add markdown preview when submitting a review
- Support no label/assignee filter and batch clearing labels/assignees
- Display when a repo was archived
- Improve squash merge commit author and co-author with private emails
- Allow adding new files to an empty repo
- Move
Rename branchfrom repo settings page to the page of branches list - Add "Updated" column for admin repositories list
- Hide the merge box of a pull request if it is merged and the branch was deleted
- The repository migration can be canceled
- Add button on the diff header to copy the file name
- Add --quiet option to the dump CLI
- Support searching for an issue with its number in the the list of issues
- Improve the list of notifications
- When editing a file in the web UI, allow for a preview whenever possible
- Make release download URLs human readable
- Add a tooltip to
Publish Reviewexplaining why they are disabled - Show the file tree view by default when browsing the changes in a pull request
- Allow both fullname search in the author dropdown search of the issue list when
DEFAULT_SHOW_FULL_NAMEis true
- Performance
- Improve performances when listing issues
- Speedup loading the list of authors in the dropdown of the list of issues
- Use minio/sha256-simd for accelerated SHA256
- Speed up HasUserStopwatch & GetActiveStopwatch
- Do not create commit graph for temporary repos
- Faster git.GetDivergingCommits
- Order pull request conflict checking by recently updated, for each push
- MySQL integration tests run twice faster low end machines and use an order of magnitude less disk I/O
- Authentication
- Refactor: Many essential sub-systems were refactored: the queue system that handles background tasks such as checking pull requests, pull mirror, git internal API, routes and web routes, merge & update logic and git command calls, listing commits, cookie, issue stats, renaming users and organizations, app.ini handling, diffFileInfo / DiffTreeStore.... In theory these changes are transparent to the Forgejo user and admin but the risk of subtle regressions is real: do not hesitate to reach out if you suspect anything.
- RSS
- API
- Add admin API for email
- Add admin API to rename a user
- Add login name and source id to admin user searching API
- Add missing units to create and edit repo API
- Add API to manage issue dependencies
- Add API for activity feeds
- Add API for license templates
- Add API for gitignore templates
- Add API to upuload a file to an empty repository
- Allow for --not when listing the commits of a repo
- Add
filesandverificationparameters to improve performances when listing the commits of a a repo - Allow for listing a single commit in a repository
- Create a branch directly from commit on the create branch API
- Add API for Label templates
- Add API for changing/creating/deleting multiple files
- Miscellaneous Features
- Any URL scheme may be used for links. Previously, non-standard URLs (like matrix:) were not rendered unless explicitly listed in
markdown.CUSTOM_URL_SCHEMES. Now the default ifmarkdown.CUSTOM_URL_SCHEMESis not set, all schemes are allowed and markdown links (label) render as links. - Always use "utf8mb4" for MySQL
- Add Adopt repository event and handler
- Add meilisearch support to index the content of repositories.
- Add support for redis v7
- Allow webp images as avatars
- Add support for rendering .livemd
- The
forgejo forgejo-cli actionssubcommand is added to implement offline registration withactions registerfor the Forgejo runner. - When called as
forgejo-cli(withln -f forgejo forgejo-cli), Forgejo provides a new CLI that is not backward compatible with Gitea. It contains Forgejo specific additions such as offline registration - Render list items when an org-mode file is displayed
- A user can follow an organization
- When playing a video in the web UI, the player control can be dragged to play on the specified position
- The commit status required for a pull request to be merged can now be specified as patterns instead of being a hard coded list
- Support wildcard in email domain allow and block lists. Read more about EMAIL_DOMAIN_ALLOWLIST and EMAIL_DOMAIN_BLOCKLIST.
- When installing with docker the value of a configuration variable can now be fetched from a file by adding the
__FILEsuffix. For instanceFORGEJO__security__INTERNAL_TOKEN__FILE=/etc/forgejo/tokencan be used instead ofFORGEJO__security__INTERNAL_TOKEN=tokenvalue. - The new
[git.config]section ofapp.iniis used togit set config. Read more about the defaults it contains. - Issues and pull requests can be pinned. They will show on top of the list of issues (or pull requests) and can be re-arranged by dragging them.
- Implement systemd-notify protocol and allows for using
Type=notifyin service files. - Provide more control over the repositories that are indexed. Read more about REPO_INDEXER_REPO_TYPES.
- Any URL scheme may be used for links. Previously, non-standard URLs (like matrix:) were not rendered unless explicitly listed in
- Webhook
- Similar to organization wide webhooks, it is now possible to have user wide webhooks
- Add webhook trigger when a Pull Request review requests is created
-
Container images upgraded to Alpine 3.18
The Forgejo container images are now based on Alpine 3.18 instead of Alpine 3.17.
1.19.4-0
The complete list of commits included in the Forgejo v1.19.4-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.19.3-0..v1.19.4-0
This stable release contains security fixes.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated from
4.2.1+0-gitea-1.19.3to4.2.2+0-gitea-1.19.4. -
Security fixes
- An additional verification was implemented to prevent open redirects.
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Fix an edge case where a user changing their
usernamein their profile page could fail - The secrets are only meaningful in the context of
Frogejo Actions, do not display them ifForgejo Actionsis disabled (patch 1, patch 2) - Actions can now be triggered on mirrored repositories (patch 1, patch 2)
- Return
404in the API if the requested webhooks were not found instead of500 - Ensure topics deleted via the API are also deleted in the repository
- Tentative fix to suppress the JavaScript error TypeError: undefined is not an object (evaluating '_i18n.textEdited') on safari. It is unclear if that fix is effective because it could not be reproduced, please report if it still happens for you.
- Respect original content when creating secrets
- If a mirror failed and left the database in an inconsistent state, make it so the repository page does not fail with an error
500 - If a user that triggered
Actionsis deleted, allow for the page listing the tasks it launched to show instead of failing with an error500 - Allow the selection of milestones when acting on multiple issues in the issue list page
- Fix the API error message when trying to create a fork that already exists
- Don't display a
create pagebutton in a mirror wiki repository. A mirrored repository will also mirror a wiki and changes will be overridden. - Do not allow for a repository to enable actions if it is not enabled in the configuration
- Allow for closed PRs to be re-opened and synchronize with the latest content of the head branch
- Fix the
closebutton of projects within an organization. It was a noop and now effectively closes the project
- Fix an edge case where a user changing their
1.19.3-0
The complete list of commits included in the Forgejo v1.19.3-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.19.2-0..v1.19.3-0
This stable release contains security fixes.
-
Recommended Action
We recommend that all Forgejo installations are upgraded to the latest version.
-
The semantic version was updated from
4.2.0+0-gitea-1.19.2to4.2.1+0-gitea-1.19.3because of the rebuild with Go version 1.20.4. -
Security fixes
- Forgejo was recompiled with Go version v1.20.4 published 2 May 2023. It fixes three vulnerabilities (CVE-2023-29400, CVE-2023-24540, CVE-2023-24539) related to the html/template package. The Forgejo security team analyzed the security fixes it contains and concluded that Forgejo is not affected but recommended a rebuild as a precaution.
-
Bug fixes
The most prominent one is described here, others can be found in the list of commits included in the release as described above.
- Allow users that are not signed in to browse the tag list. Requiring users to be signed in to view the tag list was a regression introduced in Forgejo v1.19.2-0.
1.19.2-0
The complete list of commits included in the Forgejo v1.19.2-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.19.1-0..v1.19.2-0
This stable release contains important security fixes.
-
Recommended Action
We strongly recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
-
The semantic version was updated from
4.1.0+0-gitea-1.19.1to4.2.0+0-gitea-1.19.2because of the changes introduced in the internal CI. -
Security fixes
- Token scopes were not enforced in some cases (patch 1 and patch 2). The scoped token were introduced in Forgejo v1.19 allow for the creation of application tokens that only have limited permissions, such as creating packages or accessing repositories. Prior to Forgejo v1.19 tokens could be used to perform any operation the user issuing the token could.
- Permissions to delete secrets was not enforced. The experimental internal CI relies on secrets managed via the web interface, for instance to communicate credentials to a job. Secrets are only used in the context of the experimental internal CI.
-
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Restore public access to some API endpoints. When scoped token introduced in Forgejo v1.19, some API endpoints that were previously accessible anonymously became restricted:
/orgs,/orgs/{org},/orgs/{org}/repos,/orgs/{org}/public_members,/orgs/{org}/public_members/{username},/orgs/{org}/labels. - Fix 2-dot direct compare to use the right base commit. For 2-dot direct compare, the base commit should be used in the title and templates, as is used elsewhere, not the common ancestor which is used for 3-dot compare.
- Make CORS work. No CORS headers were set, even if CORS was enabled in the configuration.
- Fix issue attachment removal. When an attachment was removed from an issue or review comment, all of the image/attachment links were broken.
- Fix wiki write permissions for users who do not have repository write permissions. When a team member had write access to the wiki but not to the code repository, some operations (deleting a page for instance) were denied.
- Respect the REGISTER_MANUAL_CONFIRM setting when registering via OAuth. Contrary to the local registration, the OAuth registration flow activated a newly registered user regardless of the value of
REGISTER_MANUAL_CONFIRM. - Fix tags list for repos whose release setting is disabled. When releases was disabled the "tags" button led to a
Not Foundpage, even when tags existed.
- Restore public access to some API endpoints. When scoped token introduced in Forgejo v1.19, some API endpoints that were previously accessible anonymously became restricted:
-
Container image upgrades
In the Forgejo container images the Git version was upgraded to 2.38.5 as a precaution. The Forgejo security team analyzed the security fixes it contains and concluded that Forgejo is not affected.
1.19.1-0
The complete list of commits included in the Forgejo v1.19.1-0 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.19.0-3..v1.19.1-0
This stable release includes bug fixes. Functional changes related to the experimental CI have also been backported.
-
Recommended Action
We recommend that all installations are upgraded to the latest version.
-
The semantic version was updated from
4.0.0+0-gitea-1.19.0to4.1.0+0-gitea-1.19.1because of the changes introduced in the internal CI. -
Bug fixes
The most prominent ones are described here, others can be found in the list of commits included in the release as described above.
- Fix RSS/ATOM/GPG/KEYS path for users (or orgs) with a dot in their name. It is allowed for a user (or an organization) to have a dot in their name, for instance
user.name. Because of a bug in Chi it was not possible to access/user.name.png,/user.name.gpg, etc. A workaround was implemented while a proper fix is being discussed. - Creating a tag via the web interface no longer requires a title.
- Use fully qualified URLs in Dockerfile. The Dockerfile to create the Forgejo container image now uses the fully qualified image
docker.io/library/golang:1.20-alpine3.17instead ofgolang:1.20-alpine3.17. This allows for building on platforms that don't have docker hub as the default container registry. - Redis use Get/Set instead of Rename when Regenerate session id. The old sid and new sid may be in different redis cluster slot.
- Do not escape space between PyPI repository url and package name. It also adds a trailing slash to the PyPI repository URL in accordance to Python PEP-503.
- Fix failure when using the API and an empty rule_name to protect a branch. The
rule_nameparameter for the /repos/{owner}/{repo}/branch_protections API now defaults to the branch name instead of being empty. - Fix branch protection priority. Contrary to the documentation it was possible for a glob rule to take precedence over a non-glob rule.
- Fix deleting an issue when the git repo does not exist. If a project had an issue tracker (such as the Forgejo discussion) but no git repository, trying to delete an issue would fail.
- Fix accidental overwriting of LDAP team memberships. If an LDAP user is a member of two groups, the LDAP group sync only matched the last group.
- Fix RSS/ATOM/GPG/KEYS path for users (or orgs) with a dot in their name. It is allowed for a user (or an organization) to have a dot in their name, for instance
1.19.0-3
The complete list of commits included in the Forgejo v1.19.0-3 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges v1.19.0-2..v1.19.0-3
This stable release includes security updates and bug fixes.
-
Recommended Action
We recommend that all installations are upgraded to the latest version.
-
Security
The Forgejo security team analyzed the vulnerabilities fixed in the latest Go 1.20.3 packages and Alpine 3.17.3 and concluded that Forgejo is not affected.
As a precaution the Forgejo v1.19.0-3 binaries were compiled with Go 1.20.3 packages as published on 4 April 2023 and the container images were built with Alpine 3.17.3 as published on 29 March 2023.
-
The semantic version was updated from
3.0.0+0-gitea-1.19.0to4.0.0+0-gitea-1.19.0because of the breaking changes described below. -
Breaking changes
They should not have a significant impact because they are related to experimental features (federation and CI).
-
Use User.ID instead of User.Name in ActivityPub API for Person IRI
The ActivityPub id is an HTTPS URI that should remain constant, even if the user changes their name.
-
Actions unit is repo.actions instead of actions.actions
All instances of
actions.actionsin theDISABLED_REPO_UNITSorDEFAULT_REPO_UNITSconfiguration variables must be replaced withrepo.actions.
-
-
Bug fixes
They are for the most part about user interface and actions. The most prominent ones are:
- Do not filter repositories by default on the explore page. The behavior of the explore page is back to what it was in Forgejo v1.18. Changing it was confusing.
- Skip LFS when disabled in dump and doctor.
- Do not display own email on the profile.
- Make minio package support legacy MD5 checksum.
- Do not triggers Webhooks and actions on closed PR.
1.19.0-2
The complete list of commits included in the Forgejo v1.19.0-2 release can be reviewed from the command line with:
$ git clone https://codeberg.org/forgejo/forgejo/
$ git -C forgejo log --oneline --no-merges origin/v1.18/forgejo..origin/v1.19/forgejo
-
Breaking changes
-
Forgejo access token, used with the API can now have a "scope" that limits what it can access. Existing tokens stored in the database and created before Forgejo v1.19 had unlimited access. For backward compatibility, their access will remain the same and they will continue to work as before. However, newly created token that do not specify a scope will now only have read-only access to public user profile and public repositories.
For instance, the
/users/{username}/tokensAPI endpoint will require thescopes: ['all', 'sudo']parameter and theforgejo admin user generate-access-tokenwill require the--scopes all,sudoargument obtain tokens with unlimited access as before for admin users. -
Disable all units except code and pulls on forks
When forking a repository, the fork will now have issues, projects, releases, packages and wiki disabled. These can be enabled in the repository settings afterwards. To change back to the previous default behavior, configure
DEFAULT_FORK_REPO_UNITSto be the same value asDEFAULT_REPO_UNITS. -
Filter repositories by default on the explore page
The explore page now always filters out repositories that are considered not relevant because they are either forks or have no topic and not description and no icon. A link is shown to display all repositories, unfiltered.
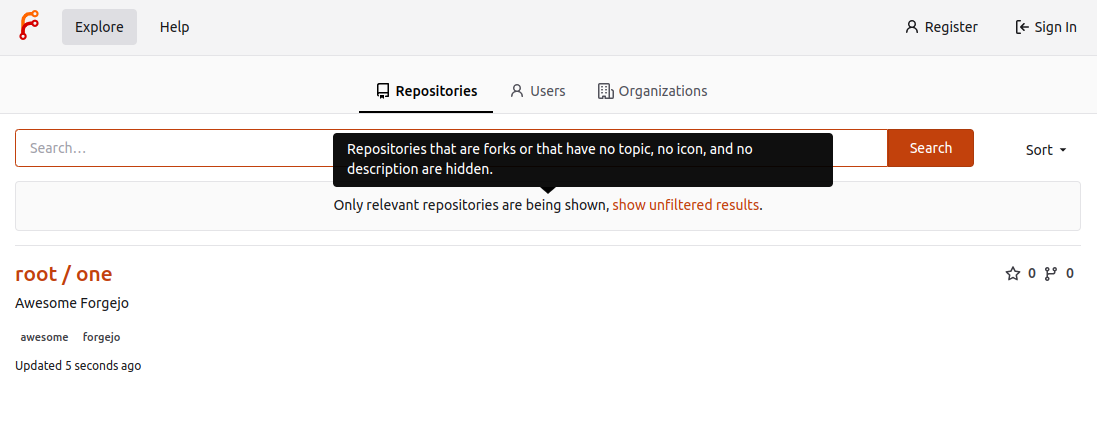
-
Remove deprecated DSA host key from Docker Container Since OpenSSH 7.0 and greater similarly disable the ssh-dss (DSA) public key algorithm, and recommend against its use. http://www.openssh.com/legacy.html
-
Additional restrictions on valid user names
The algorithm for validating user names was modified and some users may have invalid names. The command
forgejo doctor --run check-user-nameswill list all of them so they can be renamed.If a Forgejo instance has users or organizations named
forgejo-actionsandgitea-actions, they will also need to be renamed before the upgrade. They are now reserved names for the experimental internal CI/CD namedActions. -
Since v1.18.5, in addition to the Forgejo release number, a semantic version number (e.g.
v3.0.0) can be obtained from thenumberkey of a new/api/forgejo/v1/versionendpoint.Now, it reflects the Gitea version that Forgejo depends on, is no longer prefixed with
v(e.g.3.0.0+0-gitea-1.19.0), and can be obtained from theversionkey of the same endpoint.
-
-
Features
-
Documentation The first version of the Forgejo documentation is available and covers the administration of Forgejo, from installation to troubleshooting.
-
Webhook authorization header Forgejo webhooks can be configured to send an authorization header to the target.
-
Incoming emails You can now set up Forgejo to receive incoming email. When enabled, it is now possible to reply to an email notification from Forgejo and:
- Add a comment to an issue or a pull request
- Unsubscribe to the notifications
-
Packages registries
- Support for Cargo, Conda and Chef
- Cleanup rules
- Quota limits
-
Option to prohibit fork if user reached maximum limit of repositories It is possible for a user to create as many fork as they want, even when a quota on the number of repositories is imposed. The new
ALLOW_FORK_WITHOUT_MAXIMUM_LIMITsetting can now be set tofalseso forks are prohibited if that means exceeding the quota. -
Scoped labels Labels that contain a forward slash (/) separator are displayed with a slightly different color before and after the separator, as a visual aid. The first part of the label defines its "scope".
-
Support org/user level projects It is now possible to create projects (kanban boards) for an organization or a user, in the same way it was possible for an individual repository.
-
Map OIDC groups to Orgs/Teams When a user logs in Forgejo using an provider such as Keycloak, they can now automatically be part of a Forgejo team, depending on the OIDC group they belong to. For instance:
{"Developer": {"MyForgejoOrganization": ["MyForgejoTeam1", "MyForgejoTeam2"]}}Means that the user who is in the OIDC group
Developerwill automatically be a member of theMyForgejoTeam1andMyForgejoTeam2teams in theMyForgejoOrganizationorganization. This mapping is set when adding a newAuthentication Sourcein theSite Administrationpanel.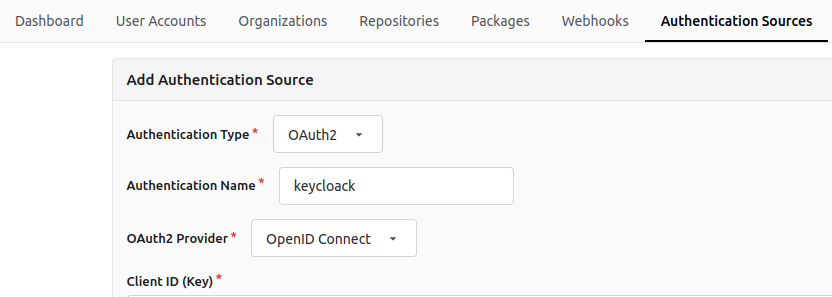
...

-
RSS feed for releases and tags
A RSS feed is now available for releases at
/{owner}/{repo}/releases.rssand tags at/{owner}/{repo}/tags.rss. -
Supports wildcard protected branch
Instead of selecting a branch to be protected, the name of the branch must be specified and can be a pattern such as
precious*. -
Garbage collect LFS Add a doctor command for full garbage collection of LFS:
forgejo doctor --run gc-lfs. -
Additions to the API
-
Option to disable releases on a repository
It is now possible to disable releases on a repository, in the same way it is possible to disable issues or packages.
-
Git reflog support The git reflog are now active by default on all repositories and kept around for 90 days. It allows the Forgejo admin to recover the previous tip of a branch after an accidental force push.
-
Actions: an experimental CI/CD
It appears for the first time in this Forgejo release but is not yet fit for production. It is not fully implemented and may be insecure. However, as long as it is not enabled, it presents no risk to existing Forgejo instances.
If a repository has a file such as
.forgejo/workflows/test.yml, it will be interpreted, for instance to run tests and verify the code in the repository works as expected (Continuous Integration). It can also be used to create HTML pages for a website and publish them (Continuous Deployment). The syntax is similar to GitHub Actions and the jobs can be controlled from the Forgejo web interface.Read more about Forgejo Actions
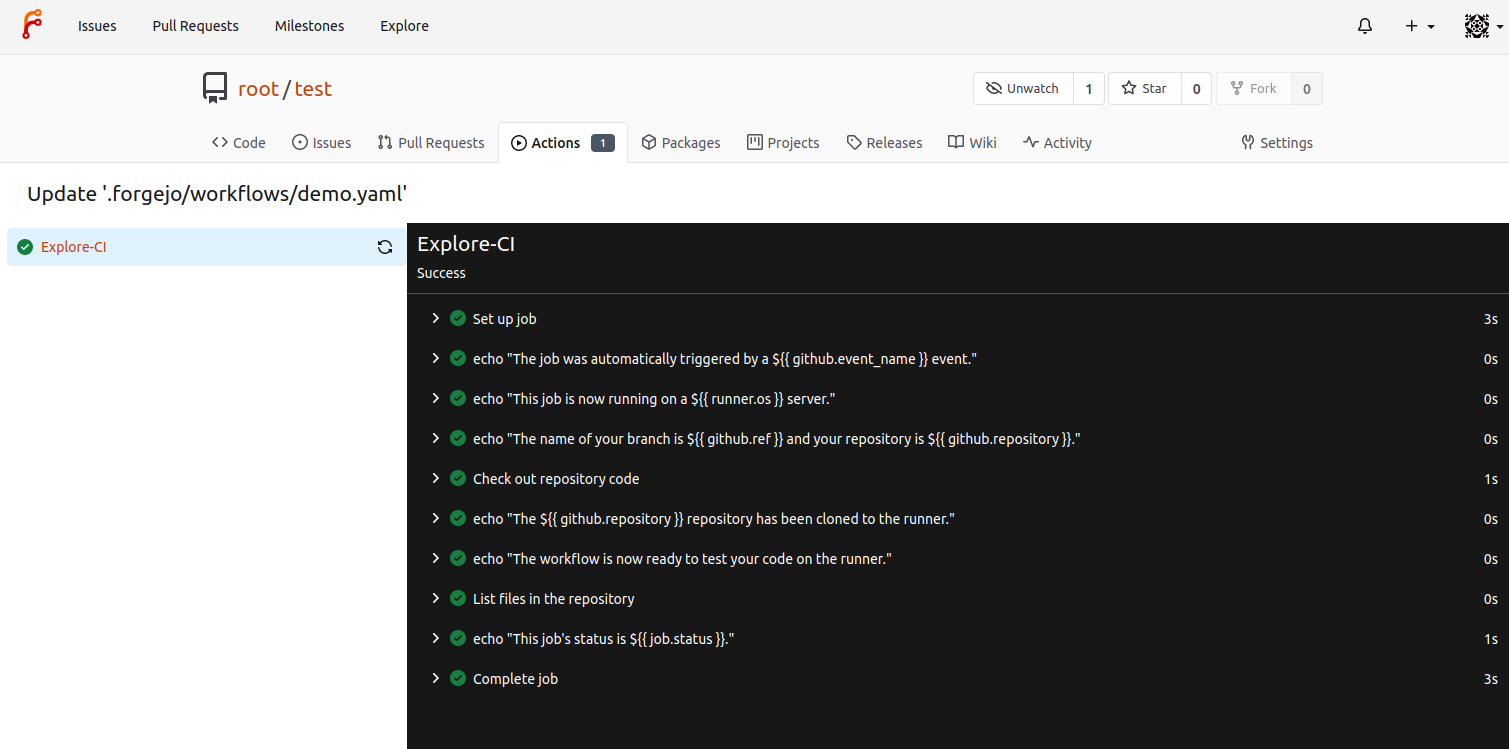
-
-
User Interface improvements
-
Review box on small screens The rendering of the review box is improved on small screens.
-
Video element enabled in markdown The
<video>HTML tag can now be used in MarkDown, with thesrc,autoplay, andcontrolsattributes. -
Copy citation file content in APA and BibTex format If a BibTeX file named
CITATION.bibis at the root of the repository, it can be conveniently copied and converted in APA by following theCite this repositorylink.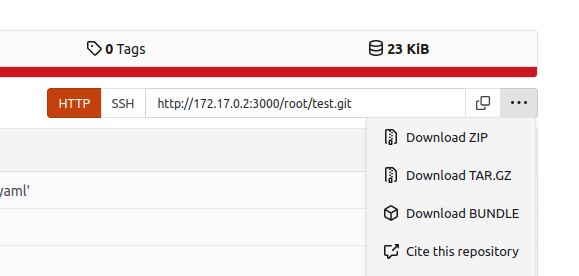
It will open a dialog box with the available formats and a preview of the content.
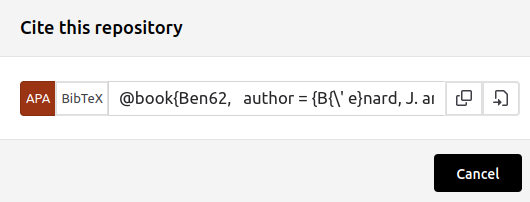
The CFF format is also supported when a
CITATION.cfffile used instead. -
Files with the
.castextension are displayed in the Forgejo web interface as asciicast v2 using asciinema-player. -
Attention blocks Note and Warning
For each quote block, the first
**Note**or**Warning**gets an icon prepended to it and its text is colored accordingly.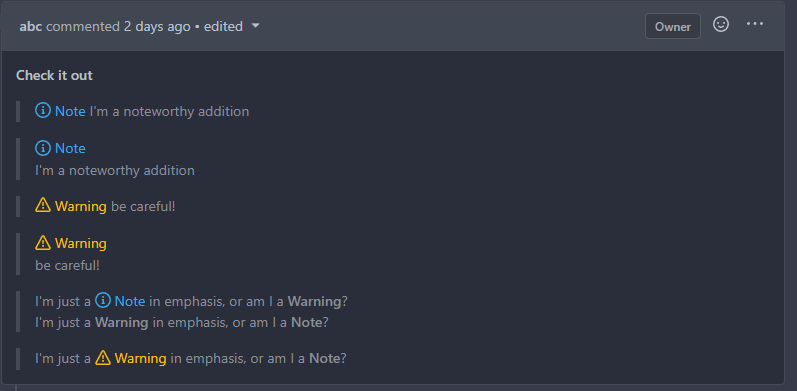
-
Support for commit cross references
A commit hash can now be prefixed by the repository to be referenced from a comment in another repository:
owner/repo@commit. -
Preview images for Issue cards in Project Board view
If the card preview in the project is set to Images and Text, it displays images found in the corresponding issue. The most recent is displayed first, up to five images.
-
Add "Copy" button to file view of raw text
If a raw text file is displayed, a copy button of the text is enabled.
Before
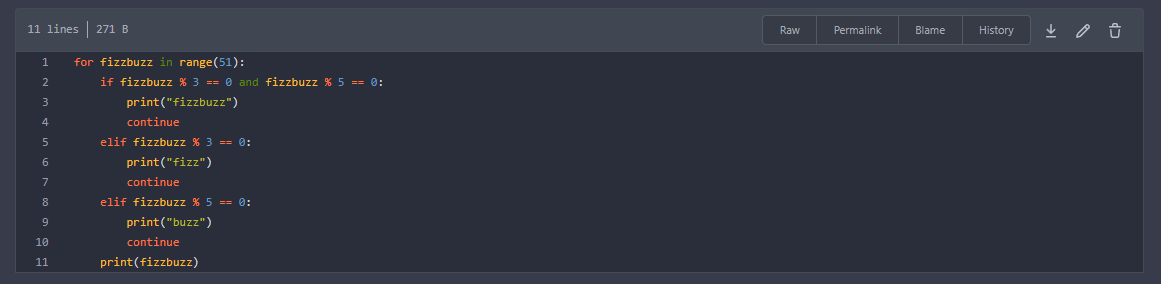
After
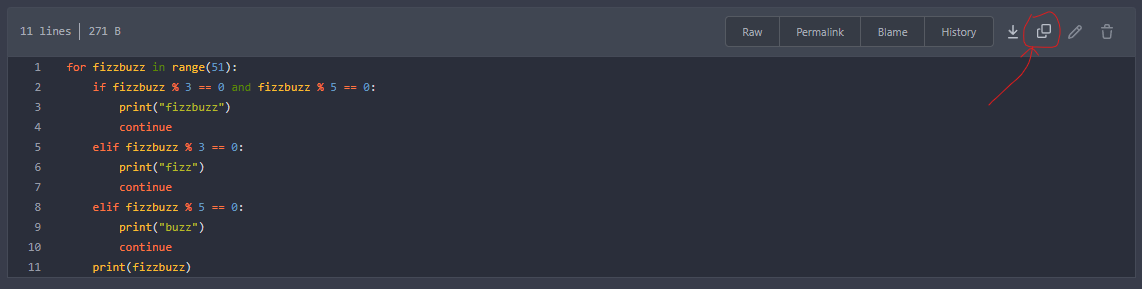
-
Setting to allow edits on PRs by maintainers
Add setting to allow edits by maintainers by default, to avoid having to often ask contributors to enable this.
-
-
Container images upgraded to Alpine 3.17
The Forgejo container images are now based on Alpine 3.17 instead of Alpine 3.16. It includes an upgrade from git 2.36.5 to git 2.38.4 and from openssh 9.0p1 to openssh 9.1p1.
1.18.5-0
This stable release contains an important security fix for Forgejo to raise the protection against brute force attack on hashed passwords stored in the database to match industry standards, as described in detail in a companion blog post.
Recommended Action
We strongly recommend that all Forgejo installations are upgraded to the latest version as soon as possible.
If PASSWORD_HASH_ALGO is explicitly set in app.ini, comment it out so that the stronger algorithm is used instead.
All password hashes stored with another algorithm will be updated to the new algorithm on the next usage of this password (e.g. a user provides the password to the Forgejo server when they login). It does not require manual intervention.
Forgejo
- SECURITY
- Upgrade the default password hash algorithm to pbkdf2 with 320,000 iterations (https://codeberg.org/forgejo/forgejo/pulls/407)
- BUGFIXES
- Return the Forgejo semantic version instead of "development" (https://codeberg.org/forgejo/forgejo/pulls/381)
Gitea
- SECURITY
- Provide the ability to set password hash algorithm parameters (https://github.com/go-gitea/gitea/pull/22942) (https://github.com/go-gitea/gitea/pull/22943)
- BUGFIXES
- Use
--message=%sfor git commit message (https://github.com/go-gitea/gitea/pull/23028) (https://github.com/go-gitea/gitea/pull/23029) - Render access log template as text instead of HTML (https://github.com/go-gitea/gitea/pull/23013) (https://github.com/go-gitea/gitea/pull/23025)
- Fix the Manually Merged form (https://github.com/go-gitea/gitea/pull/23015) (https://github.com/go-gitea/gitea/pull/23017)
- Use beforeCommit instead of baseCommit (https://github.com/go-gitea/gitea/pull/22949) (https://github.com/go-gitea/gitea/pull/22996)
- Display attachments of review comment when comment content is blank (https://github.com/go-gitea/gitea/pull/23035) (https://github.com/go-gitea/gitea/pull/23046)
- Return empty url for submodule tree entries (https://github.com/go-gitea/gitea/pull/23043) (https://github.com/go-gitea/gitea/pull/23048)
- Notify on container image create (https://github.com/go-gitea/gitea/pull/22806) (https://github.com/go-gitea/gitea/pull/22965)
- Some refactor about code comments(https://github.com/go-gitea/gitea/pull/20821) (https://github.com/go-gitea/gitea/pull/22707)
- Use
Note that there is no Forgejo v1.18.4-N because Gitea v1.18.4 was replaced by Gitea v1.18.5 a few days after its release because of a regression. Forgejo was not affected.
1.18.3-2
This stable release includes a security fix for git and bug fixes.
Git
Git recently announced new versions to address two CVEs (CVE-2023-22490, CVE-2023-23946). On 14 Februrary 2023, Git published the maintenance release v2.39.2, together with releases for older maintenance tracks v2.38.4, v2.37.6, v2.36.5, v2.35.7, v2.34.7, v2.33.7, v2.32.6, v2.31.7, and v2.30.8. All major GNU/Linux distributions also provide updated packages via their security update channels.
We recommend that all installations running a version affected by the issues described below are upgraded to the latest version as soon as possible.
- When using a Forgejo binary: upgrade the
gitpackage to a version greater or equal to v2.39.2, v2.38.4, v2.37.6, v2.36.5, v2.35.7, v2.34.7, v2.33.7, v2.32.6, v2.31.7 or v2.30.8 - When using a Forgejo container image:
docker pull codeberg.org/forgejo/forgejo:1.18.3-2
Forgejo
- BUGFIXES
- Use proxy for pull mirror (https://github.com/go-gitea/gitea/pull/22771) (https://github.com/go-gitea/gitea/pull/22772)
- Revert "Fixes accessibility of empty repository commit status" (https://github.com/go-gitea/gitea/pull/22632)
- A regression introduced in 1.18.3-1 prevented the CI status from displaying for commits with more than one pipeline
- FORGEJO RELEASE PROCESS BUGFIXES
- The tag SHA in the uploaded repository must match (https://codeberg.org/forgejo/forgejo/pulls/345) Read more about the consequences of this on the Forgejo blog
Gitea
- BUGFIXES
- Load issue before accessing index in merge message (https://github.com/go-gitea/gitea/pull/22822) (https://github.com/go-gitea/gitea/pull/22830)
- Fix isAllowed of escapeStreamer (https://github.com/go-gitea/gitea/pull/22814) (https://github.com/go-gitea/gitea/pull/22837)
- Escape filename when assemble URL (https://github.com/go-gitea/gitea/pull/22850) (https://github.com/go-gitea/gitea/pull/22871)
- Fix PR file tree folders no longer collapsing (https://github.com/go-gitea/gitea/pull/22864) (https://github.com/go-gitea/gitea/pull/22872)
- Fix incorrect role labels for migrated issues and comments (https://github.com/go-gitea/gitea/pull/22914) (https://github.com/go-gitea/gitea/pull/22923)
- Fix blame view missing lines (https://github.com/go-gitea/gitea/pull/22826) (https://github.com/go-gitea/gitea/pull/22929)
- Fix 404 error viewing the LFS file (https://github.com/go-gitea/gitea/pull/22945) (https://github.com/go-gitea/gitea/pull/22948)
- FEATURES
- Add command to bulk set must-change-password (https://github.com/go-gitea/gitea/pull/22823) (https://github.com/go-gitea/gitea/pull/22928)
1.18.3-1
This stable release includes bug fixes.
Forgejo
- ACCESSIBILITY
- Add ARIA support for Fomantic UI checkboxes (https://github.com/go-gitea/gitea/pull/22599)
- Fixes accessibility behavior of Watching, Staring and Fork buttons (https://github.com/go-gitea/gitea/pull/22634)
- Add main landmark to templates and adjust titles (https://github.com/go-gitea/gitea/pull/22670)
- Improve checkbox accessibility a bit by adding the title attribute (https://github.com/go-gitea/gitea/pull/22593)
- Improve accessibility of navigation bar and footer (https://github.com/go-gitea/gitea/pull/22635)
- PRIVACY
- Use DNS queries to figure out the latest Forgejo version (https://codeberg.org/forgejo/forgejo/pulls/278)
- BRANDING
- Change the values for the nodeinfo API to correctly identify the software as Forgejo (https://codeberg.org/forgejo/forgejo/pulls/313)
- CI
- Use tagged test environment for stable branches (https://codeberg.org/forgejo/forgejo/pulls/318)
Gitea
- BUGFIXES
- Fix missing message in git hook when pull requests disabled on fork (https://github.com/go-gitea/gitea/pull/22625) (https://github.com/go-gitea/gitea/pull/22658)
- add default user visibility to cli command "admin user create" (https://github.com/go-gitea/gitea/pull/22750) (https://github.com/go-gitea/gitea/pull/22760)
- Fix color of tertiary button on dark theme (https://github.com/go-gitea/gitea/pull/22739) (https://github.com/go-gitea/gitea/pull/22744)
- Fix restore repo bug, clarify the problem of ForeignIndex (https://github.com/go-gitea/gitea/pull/22776) (https://github.com/go-gitea/gitea/pull/22794)
- Escape path for the file list (https://github.com/go-gitea/gitea/pull/22741) (https://github.com/go-gitea/gitea/pull/22757)
- Fix bugs with WebAuthn preventing sign in and registration. (https://github.com/go-gitea/gitea/pull/22651) (https://github.com/go-gitea/gitea/pull/22721)
- PERFORMANCES
- Improve checkIfPRContentChanged (https://github.com/go-gitea/gitea/pull/22611) (https://github.com/go-gitea/gitea/pull/22644)
1.18.3-0
This stable release includes bug fixes.
Forgejo
- BUGFIXES
- Fix line spacing for plaintext previews (https://github.com/go-gitea/gitea/pull/22699) (https://github.com/go-gitea/gitea/pull/22701)
- Fix README TOC links (https://github.com/go-gitea/gitea/pull/22577) (https://github.com/go-gitea/gitea/pull/22677)
- Don't return duplicated users who can create org repo (https://github.com/go-gitea/gitea/pull/22560) (https://github.com/go-gitea/gitea/pull/22562)
- Link issue and pull requests status change in UI notifications directly to their event in the timelined view. (https://github.com/go-gitea/gitea/pull/22627) (https://github.com/go-gitea/gitea/pull/22642)
Gitea
- BUGFIXES
- Add missing close bracket in imagediff (https://github.com/go-gitea/gitea/pull/22710) (https://github.com/go-gitea/gitea/pull/22712)
- Fix wrong hint when deleting a branch successfully from pull request UI (https://github.com/go-gitea/gitea/pull/22673) (https://github.com/go-gitea/gitea/pull/22698)
- Fix missing message in git hook when pull requests disabled on fork (https://github.com/go-gitea/gitea/pull/22625) (https://github.com/go-gitea/gitea/pull/22658)
1.18.2-1
This stable release includes a security fix. It was possible to reveal a user's email address, which is problematic because users can choose to hide their email address from everyone. This was possible because the notification email for a repository transfer request to an organization included every user's email address in the owner team. This has been fixed by sending individual emails instead and the code was refactored to prevent it from happening again.
We strongly recommend that all installations are upgraded to the latest version as soon as possible.
Gitea
- BUGFIXES
- When updating by rebase we need to set the environment for head repo (https://github.com/go-gitea/gitea/pull/22535) (https://github.com/go-gitea/gitea/pull/22536)
- Mute all links in issue timeline (https://github.com/go-gitea/gitea/pull/22534)
- Truncate commit summary on repo files table. (https://github.com/go-gitea/gitea/pull/22551) (https://github.com/go-gitea/gitea/pull/22552)
- Prevent multiple
Torecipients (https://github.com/go-gitea/gitea/pull/22566) (https://github.com/go-gitea/gitea/pull/22569)
1.18.2-0
This stable release includes bug fixes.
Gitea
- BUGFIXES
- Fix issue not auto-closing when it includes a reference to a branch (https://github.com/go-gitea/gitea/pull/22514) (https://github.com/go-gitea/gitea/pull/22521)
- Fix invalid issue branch reference if not specified in template (https://github.com/go-gitea/gitea/pull/22513) (https://github.com/go-gitea/gitea/pull/22520)
- Fix 500 error viewing pull request when fork has pull requests disabled (https://github.com/go-gitea/gitea/pull/22512) (https://github.com/go-gitea/gitea/pull/22515)
- Reliable selection of admin user (https://github.com/go-gitea/gitea/pull/22509) (https://github.com/go-gitea/gitea/pull/22511)
1.18.1-0
This is the first Forgejo stable point release.
Forgejo
Critical security update for Git
Git recently announced new versions to address two CVEs (CVE-2022-23521, CVE-2022-41903). On 17 January 2023, Git published the maintenance release v2.39.1, together with releases for older maintenance tracks v2.38.3, v2.37.5, v2.36.4, v2.35.6, v2.34.6, v2.33.6, v2.32.5, v2.31.6, and v2.30.7. All major GNU/Linux distributions also provide updated packages via their security update channels.
We strongly recommend that all installations running a version affected by the issues described below are upgraded to the latest version as soon as possible.
- When using a Forgejo binary: upgrade the
gitpackage to a version greater or equal to v2.39.1, v2.38.3, v2.37.5, v2.36.4, v2.35.6, v2.34.6, v2.33.6, v2.32.5, v2.31.6, or v2.30.7 - When using a Forgejo container image:
docker pull codeberg.org/forgejo/forgejo:1.18.1-0
Read more in the Forgejo blog.
Release process stability
The release process based on Woodpecker CI was entirely reworked to be more resilient to transient errors. A new release is first uploaded into the new Forgejo experimental organization for testing purposes.
Automated end to end testing of releases was implemented with a full development cycle including the creation of a new repository and a run of CI. It relieves the user and developer from the burden of tedious manual testing.
Container environment variables
When running a container, all environment variables starting with FORGEJO__ can be used instead of GITEA__. For backward compatibility with existing scripts, it is still possible to use GITEA__ instead of FORGEJO__. For instance:
docker run --name forgejo -e FORGEJO__security__INSTALL_LOCK=true codeberg.org/forgejo/forgejo:1.18.1-0
Forgejo hook types
A new forgejo hook type is available and behaves exactly the same as the existing gitea hook type. It will be used to implement additional features specific to Forgejo in a way that will be backward compatible with Gitea.
X-Forgejo headers
Wherever a X-Gitea header is received or sent, an identical X-Forgejo is added. For instance when a notification mail is sent, the X-Forgejo-Reason header is set to explain why. Or when a webhook is sent, the X-Forgejo-Event header is set with push, tag, etc. for Woodpecker CI to decide on an action.
Look and feel fixes
The Forgejo theme was modified to take into account user feedback.
Gitea
- API
- Add
sync_on_commitoption for push mirrors api (https://github.com/go-gitea/gitea/pull/22271) (https://github.com/go-gitea/gitea/pull/22292)
- Add
- BUGFIXES
- Update
github.com/zeripath/zapx/v15(https://github.com/go-gitea/gitea/pull/22485) - Fix pull request API field
closed_atalways beingnull(https://github.com/go-gitea/gitea/pull/22482) (https://github.com/go-gitea/gitea/pull/22483) - Fix container blob mount (https://github.com/go-gitea/gitea/pull/22226) (https://github.com/go-gitea/gitea/pull/22476)
- Fix error when calculating repository size (https://github.com/go-gitea/gitea/pull/22392) (https://github.com/go-gitea/gitea/pull/22474)
- Fix Operator does not exist bug on explore page with ONLY_SHOW_RELEVANT_REPOS (https://github.com/go-gitea/gitea/pull/22454) (https://github.com/go-gitea/gitea/pull/22472)
- Fix environments for KaTeX and error reporting (https://github.com/go-gitea/gitea/pull/22453) (https://github.com/go-gitea/gitea/pull/22473)
- Remove the netgo tag for Windows build (https://github.com/go-gitea/gitea/pull/22467) (https://github.com/go-gitea/gitea/pull/22468)
- Fix migration from GitBucket (https://github.com/go-gitea/gitea/pull/22477) (https://github.com/go-gitea/gitea/pull/22465)
- Prevent panic on looking at api "git" endpoints for empty repos (https://github.com/go-gitea/gitea/pull/22457) (https://github.com/go-gitea/gitea/pull/22458)
- Fix PR status layout on mobile (https://github.com/go-gitea/gitea/pull/21547) (https://github.com/go-gitea/gitea/pull/22441)
- Fix wechatwork webhook sends empty content in PR review (https://github.com/go-gitea/gitea/pull/21762) (https://github.com/go-gitea/gitea/pull/22440)
- Remove duplicate "Actions" label in mobile view (https://github.com/go-gitea/gitea/pull/21974) (https://github.com/go-gitea/gitea/pull/22439)
- Fix leaving organization bug on user settings -> orgs (https://github.com/go-gitea/gitea/pull/21983) (https://github.com/go-gitea/gitea/pull/22438)
- Fixed colour transparency regex matching in project board sorting (https://github.com/go-gitea/gitea/pull/22092) (https://github.com/go-gitea/gitea/pull/22437)
- Correctly handle select on multiple channels in Queues (https://github.com/go-gitea/gitea/pull/22146) (https://github.com/go-gitea/gitea/pull/22428)
- Prepend refs/heads/ to issue template refs (https://github.com/go-gitea/gitea/pull/20461) (https://github.com/go-gitea/gitea/pull/22427)
- Restore function to "Show more" buttons (https://github.com/go-gitea/gitea/pull/22399) (https://github.com/go-gitea/gitea/pull/22426)
- Continue GCing other repos on error in one repo (https://github.com/go-gitea/gitea/pull/22422) (https://github.com/go-gitea/gitea/pull/22425)
- Allow HOST has no port (https://github.com/go-gitea/gitea/pull/22280) (https://github.com/go-gitea/gitea/pull/22409)
- Fix omit avatar_url in discord payload when empty (https://github.com/go-gitea/gitea/pull/22393) (https://github.com/go-gitea/gitea/pull/22394)
- Don't display stop watch top bar icon when disabled and hidden when click other place (https://github.com/go-gitea/gitea/pull/22374) (https://github.com/go-gitea/gitea/pull/22387)
- Don't lookup mail server when using sendmail (https://github.com/go-gitea/gitea/pull/22300) (https://github.com/go-gitea/gitea/pull/22383)
- Fix gravatar disable bug (https://github.com/go-gitea/gitea/pull/22337)
- Fix update settings table on install (https://github.com/go-gitea/gitea/pull/22326) (https://github.com/go-gitea/gitea/pull/22327)
- Fix sitemap (https://github.com/go-gitea/gitea/pull/22272) (https://github.com/go-gitea/gitea/pull/22320)
- Fix code search title translation (https://github.com/go-gitea/gitea/pull/22285) (https://github.com/go-gitea/gitea/pull/22316)
- Fix due date rendering the wrong date in issue (https://github.com/go-gitea/gitea/pull/22302) (https://github.com/go-gitea/gitea/pull/22306)
- Fix get system setting bug when enabled redis cache (https://github.com/go-gitea/gitea/pull/22298)
- Fix bug of DisableGravatar default value (https://github.com/go-gitea/gitea/pull/22297)
- Fix key signature error page (https://github.com/go-gitea/gitea/pull/22229) (https://github.com/go-gitea/gitea/pull/22230)
- Update
- TESTING
- Remove test session cache to reduce possible concurrent problem (https://github.com/go-gitea/gitea/pull/22199) (https://github.com/go-gitea/gitea/pull/22429)
- MISC
- Restore previous official review when an official review is deleted (https://github.com/go-gitea/gitea/pull/22449) (https://github.com/go-gitea/gitea/pull/22460)
- Log STDERR of external renderer when it fails (https://github.com/go-gitea/gitea/pull/22442) (https://github.com/go-gitea/gitea/pull/22444)
1.18.0-1
This is the first Forgejo release.
Forgejo improvements
Woodpecker CI
A new CI configuration based on Woodpecker CI was created. It is used to:
- run tests on every Forgejo pull request (compliance, unit tests and integration tests)
- publish the Forgejo v1.18.0-1 release, as binary packages for amd64, arm64 and armv6 and container images for amd64 and arm64, root and rootless
Look and feel
The default themes were replaced by Forgejo themes and the landing page was modified to display the Forgejo logo and names but the look and feel remains otherwise identical to Gitea.
Privacy
Gitea instances fetch https://dl.gitea.io/gitea/version.json weekly by default, which raises privacy concerns. In Forgejo this feature needs to be explicitly activated at installation time or by modifying the configuration file. Forgejo also provides an alternative RSS feed to be informed when a new release is published.
Gitea
- SECURITY
- Remove ReverseProxy authentication from the API (https://github.com/go-gitea/gitea/pull/22219) (https://github.com/go-gitea/gitea/pull/22251)
- Support Go Vulnerability Management (https://github.com/go-gitea/gitea/pull/21139)
- Forbid HTML string tooltips (https://github.com/go-gitea/gitea/pull/20935)
- BREAKING
- Rework mailer settings (https://github.com/go-gitea/gitea/pull/18982)
- Remove U2F support (https://github.com/go-gitea/gitea/pull/20141)
- Refactor
i18ntolocale(https://github.com/go-gitea/gitea/pull/20153) - Enable contenthash in filename for dynamic assets (https://github.com/go-gitea/gitea/pull/20813)
- FEATURES
- Add color previews in markdown (https://github.com/go-gitea/gitea/pull/21474)
- Allow package version sorting (https://github.com/go-gitea/gitea/pull/21453)
- Add support for Chocolatey/NuGet v2 API (https://github.com/go-gitea/gitea/pull/21393)
- Add API endpoint to get changed files of a PR (https://github.com/go-gitea/gitea/pull/21177)
- Add filetree on left of diff view (https://github.com/go-gitea/gitea/pull/21012)
- Support Issue forms and PR forms (https://github.com/go-gitea/gitea/pull/20987)
- Add support for Vagrant packages (https://github.com/go-gitea/gitea/pull/20930)
- Add support for
npm unpublish(https://github.com/go-gitea/gitea/pull/20688) - Add badge capabilities to users (https://github.com/go-gitea/gitea/pull/20607)
- Add issue filter for Author (https://github.com/go-gitea/gitea/pull/20578)
- Add KaTeX rendering to Markdown. (https://github.com/go-gitea/gitea/pull/20571)
- Add support for Pub packages (https://github.com/go-gitea/gitea/pull/20560)
- Support localized README (https://github.com/go-gitea/gitea/pull/20508)
- Add support mCaptcha as captcha provider (https://github.com/go-gitea/gitea/pull/20458)
- Add team member invite by email (https://github.com/go-gitea/gitea/pull/20307)
- Added email notification option to receive all own messages (https://github.com/go-gitea/gitea/pull/20179)
- Switch Unicode Escaping to a VSCode-like system (https://github.com/go-gitea/gitea/pull/19990)
- Add user/organization code search (https://github.com/go-gitea/gitea/pull/19977)
- Only show relevant repositories on explore page (https://github.com/go-gitea/gitea/pull/19361)
- User keypairs and HTTP signatures for ActivityPub federation using go-ap (https://github.com/go-gitea/gitea/pull/19133)
- Add sitemap support (https://github.com/go-gitea/gitea/pull/18407)
- Allow creation of OAuth2 applications for orgs (https://github.com/go-gitea/gitea/pull/18084)
- Add system setting table with cache and also add cache supports for user setting (https://github.com/go-gitea/gitea/pull/18058)
- Add pages to view watched repos and subscribed issues/PRs (https://github.com/go-gitea/gitea/pull/17156)
- Support Proxy protocol (https://github.com/go-gitea/gitea/pull/12527)
- Implement sync push mirror on commit (https://github.com/go-gitea/gitea/pull/19411)
- API
- Allow empty assignees on pull request edit (https://github.com/go-gitea/gitea/pull/22150) (https://github.com/go-gitea/gitea/pull/22214)
- Make external issue tracker regexp configurable via API (https://github.com/go-gitea/gitea/pull/21338)
- Add name field for org api (https://github.com/go-gitea/gitea/pull/21270)
- Show teams with no members if user is admin (https://github.com/go-gitea/gitea/pull/21204)
- Add latest commit's SHA to content response (https://github.com/go-gitea/gitea/pull/20398)
- Add allow_rebase_update, default_delete_branch_after_merge to repository api response (https://github.com/go-gitea/gitea/pull/20079)
- Add new endpoints for push mirrors management (https://github.com/go-gitea/gitea/pull/19841)
- ENHANCEMENTS
- Add setting to disable the git apply step in test patch (https://github.com/go-gitea/gitea/pull/22130) (https://github.com/go-gitea/gitea/pull/22170)
- Multiple improvements for comment edit diff (https://github.com/go-gitea/gitea/pull/21990) (https://github.com/go-gitea/gitea/pull/22007)
- Fix button in branch list, avoid unexpected page jump before restore branch actually done (https://github.com/go-gitea/gitea/pull/21562) (https://github.com/go-gitea/gitea/pull/21928)
- Fix flex layout for repo list icons (https://github.com/go-gitea/gitea/pull/21896) (https://github.com/go-gitea/gitea/pull/21920)
- Fix vertical align of committer avatar rendered by email address (https://github.com/go-gitea/gitea/pull/21884) (https://github.com/go-gitea/gitea/pull/21918)
- Fix setting HTTP headers after write (https://github.com/go-gitea/gitea/pull/21833) (https://github.com/go-gitea/gitea/pull/21877)
- Color and Style enhancements (https://github.com/go-gitea/gitea/pull/21784, #21799) (https://github.com/go-gitea/gitea/pull/21868)
- Ignore line anchor links with leading zeroes (https://github.com/go-gitea/gitea/pull/21728) (https://github.com/go-gitea/gitea/pull/21776)
- Quick fixes monaco-editor error: "vs.editor.nullLanguage" (https://github.com/go-gitea/gitea/pull/21734) (https://github.com/go-gitea/gitea/pull/21738)
- Use CSS color-scheme instead of invert (https://github.com/go-gitea/gitea/pull/21616) (https://github.com/go-gitea/gitea/pull/21623)
- Respect user's locale when rendering the date range in the repo activity page (https://github.com/go-gitea/gitea/pull/21410)
- Change
commits-tablecolumn width (https://github.com/go-gitea/gitea/pull/21564) - Refactor git command arguments and make all arguments to be safe to be used (https://github.com/go-gitea/gitea/pull/21535)
- CSS color enhancements (https://github.com/go-gitea/gitea/pull/21534)
- Add link to user profile in markdown mention only if user exists (https://github.com/go-gitea/gitea/pull/21533, #21554)
- Add option to skip index dirs (https://github.com/go-gitea/gitea/pull/21501)
- Diff file tree tweaks (https://github.com/go-gitea/gitea/pull/21446)
- Localize all timestamps (https://github.com/go-gitea/gitea/pull/21440)
- Add
codehighlighting in issue titles (https://github.com/go-gitea/gitea/pull/21432) - Use Name instead of DisplayName in LFS Lock (https://github.com/go-gitea/gitea/pull/21415)
- Consolidate more CSS colors into variables (https://github.com/go-gitea/gitea/pull/21402)
- Redirect to new repository owner (https://github.com/go-gitea/gitea/pull/21398)
- Use ISO date format instead of hard-coded English date format for date range in repo activity page (https://github.com/go-gitea/gitea/pull/21396)
- Use weighted algorithm for string matching when finding files in repo (https://github.com/go-gitea/gitea/pull/21370)
- Show private data in feeds (https://github.com/go-gitea/gitea/pull/21369)
- Refactor parseTreeEntries, speed up tree list (https://github.com/go-gitea/gitea/pull/21368)
- Add GET and DELETE endpoints for Docker blob uploads (https://github.com/go-gitea/gitea/pull/21367)
- Add nicer error handling on template compile errors (https://github.com/go-gitea/gitea/pull/21350)
- Add
stattoToCommitfunction for speed (https://github.com/go-gitea/gitea/pull/21337) - Support instance-wide OAuth2 applications (https://github.com/go-gitea/gitea/pull/21335)
- Record OAuth client type at registration (https://github.com/go-gitea/gitea/pull/21316)
- Add new CSS variables --color-accent and --color-small-accent (https://github.com/go-gitea/gitea/pull/21305)
- Improve error descriptions for unauthorized_client (https://github.com/go-gitea/gitea/pull/21292)
- Case-insensitive "find files in repo" (https://github.com/go-gitea/gitea/pull/21269)
- Consolidate more CSS rules, fix inline code on arc-green (https://github.com/go-gitea/gitea/pull/21260)
- Log real ip of requests from ssh (https://github.com/go-gitea/gitea/pull/21216)
- Save files in local storage as group readable (https://github.com/go-gitea/gitea/pull/21198)
- Enable fluid page layout on medium size viewports (https://github.com/go-gitea/gitea/pull/21178)
- File header tweaks (https://github.com/go-gitea/gitea/pull/21175)
- Added missing headers on user packages page (https://github.com/go-gitea/gitea/pull/21172)
- Display image digest for container packages (https://github.com/go-gitea/gitea/pull/21170)
- Skip dirty check for team forms (https://github.com/go-gitea/gitea/pull/21154)
- Keep path when creating a new branch (https://github.com/go-gitea/gitea/pull/21153)
- Remove fomantic image module (https://github.com/go-gitea/gitea/pull/21145)
- Make labels clickable in the comments section. (https://github.com/go-gitea/gitea/pull/21137)
- Sort branches and tags by date descending (https://github.com/go-gitea/gitea/pull/21136)
- Better repo API unit checks (https://github.com/go-gitea/gitea/pull/21130)
- Improve commit status icons (https://github.com/go-gitea/gitea/pull/21124)
- Limit length of repo description and repo url input fields (https://github.com/go-gitea/gitea/pull/21119)
- Show .editorconfig errors in frontend (https://github.com/go-gitea/gitea/pull/21088)
- Allow poster to choose reviewers (https://github.com/go-gitea/gitea/pull/21084)
- Remove black labels and CSS cleanup (https://github.com/go-gitea/gitea/pull/21003)
- Make e-mail sanity check more precise (https://github.com/go-gitea/gitea/pull/20991)
- Use native inputs in whitespace dropdown (https://github.com/go-gitea/gitea/pull/20980)
- Enhance package date display (https://github.com/go-gitea/gitea/pull/20928)
- Display total blob size of a package version (https://github.com/go-gitea/gitea/pull/20927)
- Show language name on hover (https://github.com/go-gitea/gitea/pull/20923)
- Show instructions for all generic package files (https://github.com/go-gitea/gitea/pull/20917)
- Refactor AssertExistsAndLoadBean to use generics (https://github.com/go-gitea/gitea/pull/20797)
- Move the official website link at the footer of gitea (https://github.com/go-gitea/gitea/pull/20777)
- Add support for full name in reverse proxy auth (https://github.com/go-gitea/gitea/pull/20776)
- Remove useless JS operation for relative time tooltips (https://github.com/go-gitea/gitea/pull/20756)
- Replace some icons with SVG (https://github.com/go-gitea/gitea/pull/20741)
- Change commit status icons to SVG (https://github.com/go-gitea/gitea/pull/20736)
- Improve single repo action for issue and pull requests (https://github.com/go-gitea/gitea/pull/20730)
- Allow multiple files in generic packages (https://github.com/go-gitea/gitea/pull/20661)
- Add option to create new issue from /issues page (https://github.com/go-gitea/gitea/pull/20650)
- Background color of private list-items updated (https://github.com/go-gitea/gitea/pull/20630)
- Added search input field to issue filter (https://github.com/go-gitea/gitea/pull/20623)
- Increase default item listing size
ISSUE_PAGING_NUMto 20 (https://github.com/go-gitea/gitea/pull/20547) - Modify milestone search keywords to be case insensitive again (https://github.com/go-gitea/gitea/pull/20513)
- Show hint to link package to repo when viewing empty repo package list (https://github.com/go-gitea/gitea/pull/20504)
- Add Tar ZSTD support (https://github.com/go-gitea/gitea/pull/20493)
- Make code review checkboxes clickable (https://github.com/go-gitea/gitea/pull/20481)
- Add "X-Gitea-Object-Type" header for GET
/raw/&/media/API (https://github.com/go-gitea/gitea/pull/20438) - Display project in issue list (https://github.com/go-gitea/gitea/pull/20434)
- Prepend commit message to template content when opening a new PR (https://github.com/go-gitea/gitea/pull/20429)
- Replace fomantic popup module with tippy.js (https://github.com/go-gitea/gitea/pull/20428)
- Allow to specify colors for text in markup (https://github.com/go-gitea/gitea/pull/20363)
- Allow access to the Public Organization Member lists with minimal permissions (https://github.com/go-gitea/gitea/pull/20330)
- Use default values when provided values are empty (https://github.com/go-gitea/gitea/pull/20318)
- Vertical align navbar avatar at middle (https://github.com/go-gitea/gitea/pull/20302)
- Delete cancel button in repo creation page (https://github.com/go-gitea/gitea/pull/21381)
- Include login_name in adminCreateUser response (https://github.com/go-gitea/gitea/pull/20283)
- fix: icon margin in user/settings/repos (https://github.com/go-gitea/gitea/pull/20281)
- Remove blue text on migrate page (https://github.com/go-gitea/gitea/pull/20273)
- Modify milestone search keywords to be case insensitive (https://github.com/go-gitea/gitea/pull/20266)
- Move some files into models' sub packages (https://github.com/go-gitea/gitea/pull/20262)
- Add tooltip to repo icons in explore page (https://github.com/go-gitea/gitea/pull/20241)
- Remove deprecated licenses (https://github.com/go-gitea/gitea/pull/20222)
- Webhook for Wiki changes (https://github.com/go-gitea/gitea/pull/20219)
- Share HTML template renderers and create a watcher framework (https://github.com/go-gitea/gitea/pull/20218)
- Allow enable LDAP source and disable user sync via CLI (https://github.com/go-gitea/gitea/pull/20206)
- Adds a checkbox to select all issues/PRs (https://github.com/go-gitea/gitea/pull/20177)
- Refactor
i18ntolocale(https://github.com/go-gitea/gitea/pull/20153) - Disable status checks in template if none found (https://github.com/go-gitea/gitea/pull/20088)
- Allow manager logging to set SQL (https://github.com/go-gitea/gitea/pull/20064)
- Add order by for assignee no sort issue (https://github.com/go-gitea/gitea/pull/20053)
- Take a stab at porting existing components to Vue3 (https://github.com/go-gitea/gitea/pull/20044)
- Add doctor command to write commit-graphs (https://github.com/go-gitea/gitea/pull/20007)
- Add support for authentication based on reverse proxy email (https://github.com/go-gitea/gitea/pull/19949)
- Enable spellcheck for EasyMDE, use contenteditable mode (https://github.com/go-gitea/gitea/pull/19776)
- Allow specifying SECRET_KEY_URI, similar to INTERNAL_TOKEN_URI (https://github.com/go-gitea/gitea/pull/19663)
- Rework mailer settings (https://github.com/go-gitea/gitea/pull/18982)
- Add option to purge users (https://github.com/go-gitea/gitea/pull/18064)
- Add author search input (https://github.com/go-gitea/gitea/pull/21246)
- Make rss/atom identifier globally unique (https://github.com/go-gitea/gitea/pull/21550)
- BUGFIXES
- Auth interface return error when verify failure (https://github.com/go-gitea/gitea/pull/22119) (https://github.com/go-gitea/gitea/pull/22259)
- Use complete SHA to create and query commit status (https://github.com/go-gitea/gitea/pull/22244) (https://github.com/go-gitea/gitea/pull/22257)
- Update bleve and zapx to fix unaligned atomic (https://github.com/go-gitea/gitea/pull/22031) (https://github.com/go-gitea/gitea/pull/22218)
- Prevent panic in doctor command when running default checks (https://github.com/go-gitea/gitea/pull/21791) (https://github.com/go-gitea/gitea/pull/21807)
- Load GitRepo in API before deleting issue (https://github.com/go-gitea/gitea/pull/21720) (https://github.com/go-gitea/gitea/pull/21796)
- Ignore line anchor links with leading zeroes (https://github.com/go-gitea/gitea/pull/21728) (https://github.com/go-gitea/gitea/pull/21776)
- Set last login when activating account (https://github.com/go-gitea/gitea/pull/21731) (https://github.com/go-gitea/gitea/pull/21755)
- Fix UI language switching bug (https://github.com/go-gitea/gitea/pull/21597) (https://github.com/go-gitea/gitea/pull/21749)
- Quick fixes monaco-editor error: "vs.editor.nullLanguage" (https://github.com/go-gitea/gitea/pull/21734) (https://github.com/go-gitea/gitea/pull/21738)
- Allow local package identifiers for PyPI packages (https://github.com/go-gitea/gitea/pull/21690) (https://github.com/go-gitea/gitea/pull/21727)
- Deal with markdown template without metadata (https://github.com/go-gitea/gitea/pull/21639) (https://github.com/go-gitea/gitea/pull/21654)
- Fix opaque background on mermaid diagrams (https://github.com/go-gitea/gitea/pull/21642) (https://github.com/go-gitea/gitea/pull/21652)
- Fix repository adoption on Windows (https://github.com/go-gitea/gitea/pull/21646) (https://github.com/go-gitea/gitea/pull/21650)
- Sync git hooks when config file path changed (https://github.com/go-gitea/gitea/pull/21619) (https://github.com/go-gitea/gitea/pull/21626)
- Fix 500 on PR files API (https://github.com/go-gitea/gitea/pull/21602) (https://github.com/go-gitea/gitea/pull/21607)
- Fix
Timestamp.IsZero(https://github.com/go-gitea/gitea/pull/21593) (https://github.com/go-gitea/gitea/pull/21603) - Fix viewing user subscriptions (https://github.com/go-gitea/gitea/pull/21482)
- Fix mermaid-related bugs (https://github.com/go-gitea/gitea/pull/21431)
- Fix branch dropdown shifting on page load (https://github.com/go-gitea/gitea/pull/21428)
- Fix default theme-auto selector when nologin (https://github.com/go-gitea/gitea/pull/21346)
- Fix and improve incorrect error messages (https://github.com/go-gitea/gitea/pull/21342)
- Fix formatted link for PR review notifications to matrix (https://github.com/go-gitea/gitea/pull/21319)
- Center-aligning content of WebAuthN page (https://github.com/go-gitea/gitea/pull/21127)
- Remove follow from commits by file (https://github.com/go-gitea/gitea/pull/20765)
- Fix commit status popup (https://github.com/go-gitea/gitea/pull/20737)
- Fix init mail render logic (https://github.com/go-gitea/gitea/pull/20704)
- Use correct page size for link header pagination (https://github.com/go-gitea/gitea/pull/20546)
- Preserve unix socket file (https://github.com/go-gitea/gitea/pull/20499)
- Use tippy.js for context popup (https://github.com/go-gitea/gitea/pull/20393)
- Add missing parameter for error in log message (https://github.com/go-gitea/gitea/pull/20144)
- Do not allow organisation owners add themselves as collaborator (https://github.com/go-gitea/gitea/pull/20043)
- Rework file highlight rendering and fix yaml copy-paste (https://github.com/go-gitea/gitea/pull/19967)
- Improve code diff highlight, fix incorrect rendered diff result (https://github.com/go-gitea/gitea/pull/19958)
- TESTING
- Improve OAuth integration tests (https://github.com/go-gitea/gitea/pull/21390)
- Add playwright tests (https://github.com/go-gitea/gitea/pull/20123)
- BUILD
- Switch to building with go1.19 (https://github.com/go-gitea/gitea/pull/20695)
- Update JS dependencies, adjust eslint (https://github.com/go-gitea/gitea/pull/20659)
- Add more linters to improve code readability (https://github.com/go-gitea/gitea/pull/19989)
1.18.0-0
This release was replaced by 1.18.0-1 a few hours after being published because the release process was interrupted.
1.18.0-rc1-2
This is the first Forgejo release candidate.